The dark web isn’t something you can just stumble upon, and that’s a good thing. Sites on the dark web can contain potentially catastrophic pitfalls in the form of illegal activity, phishing links, financial scams, and malware infections. There’s also little to no recourse to be had if you encounter any trouble there, because the dark web is a decentralized collection of websites hidden from search engines. It’s the side of the internet that’s used for transactions and conversations that need to stay anonymous.
Deep Web Vs Dark Web Vs Surface Web
- There are also many tools that can be use to monitor the dark web and scan for personally identifiable information and even respond to attacks.
- The deep web means every section of the internet is inaccessible by regular search engines.
- The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address.
- However, there are some significant variances in the background despite the similarities.
- You can use the VPN rated #1 for the dark web with no restrictions for a month—great if you want to try this no-log provider’s Onion over VPN servers for yourself.
The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. Many people see hacked information and stolen card data being sold on the dark web. However, you can find legitimate content and activities here, too. For example, you can find information unavailable to the public and share data privately while protecting your online identity. Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies. Talking about copycats and potential risks, due to its high risk and low signal-to-noise ratio for legitimate content, we advise beginners and privacy-conscious users to avoid The Hidden Wiki.
You should stay away from everything labeled “porn”, “card skimming services”, “PayPal hacks”, “firearms”, “real fake IDs and passports”. Believe me – there are plenty to go around and each and every one of them are being kept under surveillance. Not to mention the fact that you’ll get exposed to some stuff that will definitely make you take several cold showers. Fortunately, in Hidden Wiki, every website is followed by a brief description so that the user knows what to expect.
As much as the dark web is supposed to promote free speech alongside bypassing censorship, many shady activities occur there. Removing your sensitive personal information from the dark web once it has been exposed is virtually impossible. This irreversible process highlights the importance of taking preventive measures by utilizing a service that monitors your data for potential breaches. The encrypted data, such as WhatsApp messages, are secured behind end-to-end encryption and are not visible to your ISP.
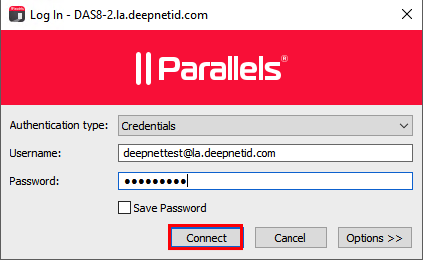
Tor Links
You need a specialized browser that encrypts your traffic, hides your IP, and makes your activity on these networks virtually invisible. Well, almost invisible—because the best practice is to combine that browser with a good VPN to strengthen your protection. By following these steps, you enter the Dark Web with more confidence and preparedness. Although it’s not inherently illegal to access the Dark Web, remember that certain sites and activities may be. Stay vigilant, trust your instincts, verify sources, and prioritize your security to make the most of the anonymity these networks provide. Now that you understand the essentials of anonymous networks and how to prepare yourself for secure browsing, it’s time to explore the practical steps involved in accessing the Dark Web.
It All Starts With A Solid Foundation Of IT Support Services
Above all, it’s vital to go on the dark web carefully and sensically. The entry node encrypts your traffic and it bounces across several nodes in the Tor networks until it reaches the exit node. This node decrypts your traffic and it reaches the destination i.e. the website you want to visit.

Best Dark Web Sites 2025 – Detailed List
- The dark web has several convenient uses, which are not all basic.
- Later, Tor’s underlying code was released under a free license, and a nonprofit called the Tor Project was formed.
- A study by researchers at King’s College London that examined the contents of over 2,700 darknet sites found that approximately 60% of them hosted illicit content.
- Anonymity is powerful with Tor and the framework of the dark web, but it is not infallible.
- Locating surface web websites is possible because search engines can index the web via visible links (a process called “crawling” due to the search engine traveling the web like a spider).
It hosts both legal and illegal activities, offering anonymity but also posing risks like scams and illicit content. Many people use Tor to avoid surveillance by government agencies, ISPs, or other entities monitoring online activities. Similarly, people in countries with strict internet access and usage regulations must use Tor clients or virtual private networks (VPNs) to access some public websites. The “Dark Web” often conjures up images of hidden marketplaces, illicit trades, and shadowy figures lurking in the digital underworld. The Dark Web is simply a part of the internet that cannot be reached by standard search engines and browsers.
Minimize Or Rescale Your Tor Browsing Window
However, note that the site only uses non-sensitive and public data for the metrics. The Tor Metrics is a good place to get more information about the Tor project. It collects data from the public Tor network and archives historical data of the Tor ecosystem. In most cases, whistleblowers have sensitive information about the government or a company.
Security Links
Additionally, you can opt for Subgraph OS as a second option to Tor. While it might appear tempting to venture into the dark web, it’s crucial to understand that the risks here are far more severe compared to the deep web. Therefore, if you do decide to explore it, exercise extreme caution. As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web. No user names are tied to actual identities, and no moderation like one may find on Reddit.

Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin. Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy. The dark web isn’t just one sketchy marketplace hiding in a corner of the internet; it’s more like a messy, unregulated community with everything from freedom fighters to full-blown cybercriminals.
Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too. It’s, ironically, more conspicuous than using popular browsers and sites. Because of its anonymity, the dark web is filled with illegal services and is used by numerous criminal groups, including ransomware gangs. It is also used by whistle-blowers, journalists, and other individuals who are not involved in illegal activity but need to protect their communications and identities.
Use A Dark Web Search Engine
The Tor network is operated by thousands of volunteers worldwide who maintain the proxy servers that protect your identity. You can download the Tor Browser for Windows, MacOS, Linux, and Android. ZDNET tested the best VPNs available based on speed, number of servers, security features, price, and more. ExpressVPN is our pick for the best VPN overall, thanks to its fast and reliable connection and the wide range of platforms it works on. It will route your traffic through multiple servers instead of one, making tracking your data and activities even harder. Since Tor has to pass your traffic through several nodes, it will slightly slow your speeds.