The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address. While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings.
Tor-Browser: Dein Zugangspunkt Zum Dark Web
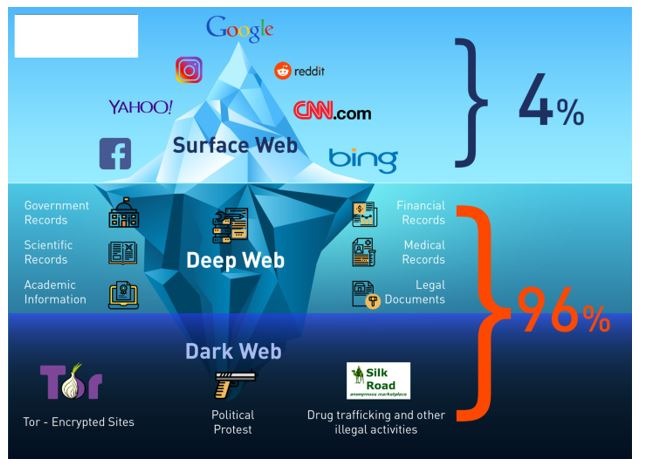
There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale. Not every visitor is a criminal, but this is where most cybercrimes begin. No user names are tied to actual identities, and no moderation like one may find on Reddit. Users leverage these platforms to organize protests, whistleblow, share survival guides, or share files P2P. The good news is that the platform will not see what you copy/paste.
The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. It will encrypt your traffic and data so no one can intercept it. For this reason, you must watch out and avoid opening anything that looks suspicious to you.
Zugang Mit Dem Tor-Browser
Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed. Besides, victims of crime may want to hide their identities from their perpetrators. Nonetheless, if whatever you do is deemed illegal in your country, you can get into trouble. Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. Simply put, accessing and browsing the dark web is perfectly legal.
Step By Step: Tor Browser Installieren Und Konfigurieren
It offers top-of-the-line security and fast speeds for a smooth browsing experience on the dark web. A reliable, fast, and user-friendly VPN service offering lots of customizable options for privacy geeks. Also, use an effective antivirus program to check threats if you decide to download files. You can check out this guide on the best antivirus software applications today. ActiveX and Java frameworks are susceptible to being exploited by hackers.
Is Using The Tor Network Illegal?
You can also check out this ultimate dark web safety guide to browse safely. If you get a reliable vendor, you should procure the services to stay safe when accessing the dark web. You can also run a dark web scan to see if your information has been leaked on the dark web. This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks. Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages.

Most likely, the native account on your device has full admin permissions by default. Many malware take advantage of this vulnerability to launch an attack. Therefore, you can prevent this exploitation by setting up a non-admin account. Many services that are allegedly offered on the dark web are scams. Some services are genuine; you can get what you want at an agreed fee. It’s important to note that although the dark web has many valuable services, it is also a hangout for cybercriminals.

Was Unterscheidet Den Tor Browser Von Einem VPN-Dienst?
The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China. It will make your VPN activities seem like normal traffic, so you can use an uncensored internet. However, this feature is only available on iOS, Android, and Windows. A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want.
Wofür Werden Onion-Seiten Verwendet?
This means you have to know someone who is already using the platform. Even without the code, you can visit the security section to get tips on improving your daily life privacy. ProtonMail is a Swiss-based email service that is very easy to use. You are not required to provide your personal information to create an account. The email service is available both on the surface and on the dark web.
- There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale.
- Additionally, you can opt for Subgraph OS as a second option to Tor.
- This will help you to remain anonymous and secure at all Tor entry and exit nodes.
- With the onion browser, you can access ordinary HTTPS websites on the web.
While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity. That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy. You risk being targeted for attacks if you explore the dark web without protection.
- Unlike other search engines, it does not collect or share web activities and personal data of users.
- Everything you find on the dark web is not necessarily illegal.
- However, note that the site only uses non-sensitive and public data for the metrics.
- The use of the dark web raises suspicion as it shows there is something you want to do privately.
- So don’t be surprised if you encounter different versions that claim to be genuine, and be very careful.
- It is easily accessible by the general public and requires no special configuration.
Featured Articles
Facebook’s dark web version allows users to access the site where it is banned or restricted. Although the social application is known for collecting data on its platform, it does not like sharing the information with others. If you know the right websites, you can easily access a tremendous amount of information, including research articles, news stories, and more.
You should never use your personal information on the dark web anywhere else in your life. In fact, create new throwaway accounts and documents if possible. Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web.
Verschleiert Tor Meine IP-Adresse?
Accessing blocked content can result in being placed on a watch list or imprisonment. Unfortunately, others are fake and fraudulent websites that exploit the reputation of the dark web to con people. Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion. All in all, it is not illegal to access the dark web, but it can create issues for you. If you don’t take the necessary measures, many unsavory activities can expose you to unnecessary risks.