
These onion addresses will remain online even if the original page disappears. It also keeps the graphical copy and text of the page for better accuracy. It is the dark web’s version of Wikipedia with a massive links directory. You will find all the necessary .onion links to access any content or service on the dark web. If you know the right websites, you can easily access a tremendous amount of information, including research articles, news stories, and more. This marketplace focuses on selling stolen financial data, such as BINs (Bank Identification Numbers), RDP/VDS access, and verified crypto accounts for money laundering.
Secure Communication And Collaboration Tools
For individuals and organizations trying to protect themselves, relying solely on conventional KYC protocols may no longer be enough. Businesses are advised to use identity management software and multi-layered verification systems for stronger protection. Whether in-store or online, the platform delivers real-time ID verification that enhances customer trust without slowing down the transaction experience. More businesses are pairing cutting-edge scanning devices with AI-driven detection systems. These tools can analyze data patterns, flag inconsistencies invisible to the human eye, and adapt as fraud techniques evolve.
- Dark web marketplaces, encrypted messaging apps, and 3D printing have enabled fraudsters to produce realistic-looking IDs at a low cost.
- This Ethereum-based counterfeit system made it so that 68 out of the 92 fake IDs seized by Toronto police in January 2025 were untraceable.
- It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last.
- In Latin America, driving licenses are most vulnerable, with a fraud rate of 1.63%, followed by visas at 2.70%, reflecting a distinct focus on forgery.
- The market frequently makes headlines for releasing massive troves of stolen data, often as a way to advertise its services.
Data And Document Compilation
Fraudsters use synthetic documents to open accounts with banks, fintech apps, and cryptocurrency exchanges. They use these accounts to apply for loans, move illicit funds, or launder money without triggering identity verification flags. Because the IDs appear authentic and pass automated checks, fraudsters often create accounts at scale before detection systems catch up. One example is ProKYC, which has been linked to a variety of synthetic fraud services. Reports indicate it provides not only fake documents but also videos designed to pass liveness checks and selfie verification workflows. According to the Cato Network, footage from Telegram channels shows ProKYC simulating full identity verification steps, posing a serious risk to platforms that rely on webcam or phone-based authentication.
With our extensive experience, you can feel confident knowing your fake ID is in the hands of skilled experts who value quality above all else. We’re not amateurs—we’re seasoned pros who guarantee results every time. Of the third-party database checks run, DMV checks were able to catch 100% of the fake IDs.
Facebook Onion Site
The Gullah Society is dedicated to preserving and celebrating the rich cultural heritage of the Gullah people. Through education, community initiatives, and cultural events, we strive to honor and promote the unique traditions and contributions of the Gullah community. Stay updated with the latest news, events, and stories from The Gullah Society. In short, fake ID statistics in 2026 are more than just numbers—they are tools for action, education, and prevention. For more information on how to protect your business from fraud, reach out to one of ComplyCube’s compliance experts.
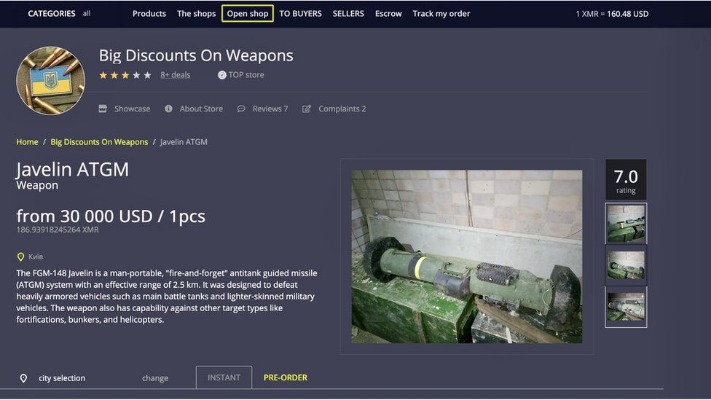
Yet, the profitability of this underground economy allows it to persist. Websites based in countries with relaxed enforcement can rake in tens of thousands of dollars monthly by selling IDs to students across the globe (Deffenbacher, 2016). As governments introduce new security measures, counterfeiters adapt quickly. These markets sell a range of illegal goods and services, including drugs, weapons, stolen data, and counterfeit items, and they typically require special software like Tor for access.

The Multi-Layered Mitigations Required To Fend Off Evolving Dark Web Identity Attack Resources
In recent years, the acquisition of fake identification (fake IDs) has become increasingly… By reading our instructions page you can pay using your Credit or Debit card by buying various forms of Gift cards. Real IDs are the newest cards to appear in the United States, and the country is currently working towards transitioning all citizens to use Real IDs. Within one or two years, the real IDs will be the new standard, and we will prepare for the next wave of improved state-issued cards.
This fragmented approach makes it nearly impossible to establish a universal defense without coordinated industry standards or updated regulatory frameworks. CFEs and anti-fraud professionals must understand how AI-powered fraud schemes operate in order to detect and prevent them effectively. Without proper safeguards, organizations may become unwitting victims of identity-related fraud, risking financial losses, reputational damage, and compromised customer trust. Fake IDs threaten national security, necessitating vigilance from authorities and public cooperation to maintain trust in identity verification processes.
Ethical And Moral Considerations Of Using Fake IDs And Documents
- Operations conducted via idbook.ph, with payments in Bitcoin, leveraging encryption to avoid detection.
- NordVPN is one of the best VPNs to combine with the Tor browser whenever you want to surf dark sites.
- For a fake ID to pass front and back inspection, both sides must align perfectly in design, data encoding, and material quality.
- At the center of this transformation is generative AI, the powerful force that redefines both offense and defense in the world of digital identity.
- It has an active forum and community along with an extensive user vetting process.
In the U.S., several states have passed new legislation targeting online fake ID sellers and increasing surveillance of digital marketplaces. They come with encoded magnetic strips, RFID chips, and barcodes that mimic legitimate data. These features allow fakes to pass basic verification scans at clubs, bars, and retail establishments.
For several years, Yahoo was at the apex as the internet’s best web service provider, offering… It will route your traffic through multiple servers instead of one, making tracking your data and activities even harder. If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic. It is a relatively new provider but offers better features than most established VPNs.
How To Use Fake IDs Safely (If At All)
These holograms vary by state, making it essential to know the specific design for your ID. For example, Illinois driver’s licenses display the state name diagonally across the front when tilted under light. In 2026, local police, federal agencies, and even international bodies are collaborating to maintain shared databases of seized fake IDs. This cooperative approach helps track large-scale operations and prevent repeat offenders from exploiting weak systems. It hosted over 7,000 .onion categorized links to make surfing the web easier.
Instead, you need a specific configuration, software, or authorization, such as Tor, to access it. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data. Blockchain.info (now Blockchain.com) is a popular cryptocurrency wallet and blockchain explorer service (one of the first sites to launch on the dark web). It was initially created to provide additional security and eliminate cryptocurrency theft. It’s a wallet, explorer service, not a dark web marketplace itself, but still a helpful resource. Established in 2012, the platform is a time capsule that collects snapshots of websites.

The primary purpose of these fake IDs is to deceive institutions or individuals into believing the holder is of legal age or identity to access services or goods. Fake IDs are often used for activities like entering clubs, purchasing alcohol, or accessing age-restricted venues. Fake IDs are a growing concern for businesses, law enforcement, and individuals alike. With the rise of advanced technology, creating high-quality fake IDs has become increasingly easier. These counterfeit IDs can be used for various purposes, including identity theft, underage drinking, and financial fraud.
Third Party Checks, Such As DMV Checks
Many social media platforms keep their presence on the dark web, and it is no surprise that Facebook has a .onion portal. Facebook’s dark web version allows users to access the site where it is banned or restricted. Although the social application is known for collecting data on its platform, it does not like sharing the information with others. The website has an advanced search filter and an easy-to-use interface, which makes it easy to find what someone is looking for. Whether local or international goods, research documents, banned drugs, you name it, everything is available on this dark web platform (that’s one of the reasons why this should be monitored for security purposes).
BBC Tor Mirror
Airports, banks, and service centers often rely on manual checks, but high error rates and document fatigue have led many institutions to phase out this method. Some airports have already moved away from manual ID inspections entirely, and financial institutions are increasingly turning to automated alternatives. Once the model is trained, it can produce entirely new IDs based on user input.



