The search engine provides several special features beyond the original word. These include weather forecasts, maps, calculations and Boolean operations as inclusion or alternatives among others. Adamant offers blockchain-based secure messaging without needing phone numbers or email addresses.
Related Articles From The Safe Browsing Section
Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. Indeed, most nations; including the United States, the United Kingdom, and India, allow access to the dark web as a lawful activity. People often have bad feelings about the dark web, but not everything on it is illegal or dangerous. In fact, journalists, privacy advocates and academics use it every day to protect their identities and get to material that has not been blocked. Whether you are doing research, applying OSINT (Open Source Intelligence), or trying to get your head around what Dark Net really is.
Directory Of Open Access Journals
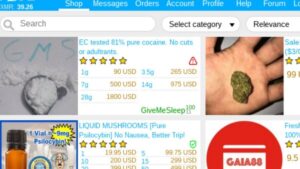
Regardless of the browser’s anonymity, it is still illegal to commit fraud or engage in any illegal activity on the dark web. According to a 2020 estimate conducted by Prey Project (a security service platform), 57% of the dark web is illegal. Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links.

What Is A Tor Browser?
That’s why security teams need continued visibility into the dark web which enables them to mitigate the risk of data leaks, preventing further damage. Cybercriminals often leverage the anonymity to leak sensitive information, like stolen credentials, credit card numbers, or company data. This process makes tracing the user’s location and activity nearly impossible. The core functionality of the dark web relies on onion routing, a method that encrypts and routes user communications across multiple servers, known as nodes. It has a reputation for being fast and effective, though the content it indexes varies widely in quality and legality. Some sites might use these details for advertising, analytics, or tracking your online preferences.
Common Use Cases For Torch Darknet Search Engine
Haystak is used to search dark web marketplaces, leaked databases, and darknet forums, often by cybersecurity experts. As a result, the dark web has become a breeding ground for illicit activities because government agencies face significant challenges in identifying the operators behind hidden services. Haystack is a dark web search engine designed with privacy in mind, similar to Duck Duck Go. Yes, you can still be tracked on the dark web despite its privacy features. Tracking can happen through IP leaks, browser vulnerabilities, or malicious exit nodes. To reduce this risk, use the Tor Browser properly, keep your software updated, avoid sharing personal information, and pair it with a reliable VPN.
- It stands as one of the most prevalent search engines utilized within the TOR Browser ecosystem.
- While many dark marketplaces have been shut down by authorities, new ones soon appear in their place.
- We review and list tools and products without bias, regardless of potential commissions.
- However, users must still connect to the dark web to visit these sites through Tor.
However, you can find legitimate content and activities here, too. For example, you can find information unavailable to the public and share data privately while protecting your online identity. Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies. It is easily accessible by the general public and requires no special configuration.
Securing Your Privacy And Safety With Dark Web Search Engines
Future engines may integrate blockchain-based reputation systems, allowing users to rate .onion sites anonymously. This would enhance safety for beginners, though maintaining anonymity in rating systems remains a technical hurdle. Machine learning is transforming dark web search engines, with Haystak already leveraging AI for result ranking and spam detection. By 2027, engines like NotEvil could adopt AI to enhance community-based filtering, identifying abusive content with greater accuracy. DeepSearch (2020) shifted toward precision, indexing a curated ~5,000 sites for targeted queries, appealing to technical researchers and journalists. This period saw dark web search engines diversify, catering to varied user needs—scale, safety, and accuracy.
VirusTotal Explained How To Scan Files And URLs For Malware Using 70

Note that engaging with the content in any way is not only distressing but could also put you at legal risk. This is because law enforcement often actively monitors these sites. While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity. That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy. You risk being targeted for attacks if you explore the dark web without protection.
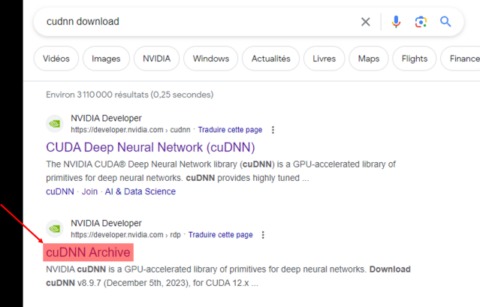
Dark web working logic We need to perform special crawling operations to index and index sites with .onion extension. It scans for keywords and topics and uses algorithms to deliver relevant pages. The Tor Browser, as we know it, is available for Windows, macOS, Linux, and Android. To download the Tor Browser, visit the official website at Torproject.org. Once you’re on the website, click “Download Tor Browser.” Then, select the appropriate version for your operating system and follow the prompts to complete the installation.
But because it’s not regulated, it’s also a potentially attractive place for cybercriminals to hang out. That’s why it’s important to be extra careful when browsing the dark web—sites you can find there may host sensitive content, foster illegal activity, or pose security threats. However, there are steps you can take to stay safer on the dark web, including never sharing personal info, using a VPN, and installing antivirus software. In this blog, we explore the top 10 Dark Web search engines of 2025, focusing on safety, anonymity, and usability. Whether you’re a journalist, researcher, cybersecurity professional, or just curious, these platforms can help you navigate the deep corners of the internet — carefully and securely.
Dark Web Vs Deep Web
- We don’t track what you’re searching for and tailor results based on that, you see what anyone else would see.
- Candle is a lightweight, open-source dark web search engine with basic search functionality and high speed.
- Install Norton VPN to encrypt your internet connection and help protect the data you share online.
- If you only want to mask your IP address and don’t need to access the dark web, then going online with a VPN is much easier and faster than using Tor.
- DuckDuckGo has a simple interface, with a search box in the middle of the page, and its list of search results is also formatted like Google’s.
It also includes any content that its owners have blocked web crawlers from indexing. This search engine’s mission is to be leaders in providing services on the deep web, protecting the anonymity of each user. In addition, they share information of great importance, about the Tor network and the Tor project.
You will find all the necessary .onion links to access any content or service on the dark web. No, Google and other search engines available on the regular part of the internet do not index .onion domains or any part of the Tor network. The dark web is intentionally hidden from surface web indexing, and to access it, you need a specialized dark web browser, like the Tor browser. If one tries to visit the dark web with a regular browser, there will be no web pages to visit.