
However, note that the site only uses non-sensitive and public data for the metrics. The Tor Metrics is a good place to get more information about the Tor project. It collects data from the public Tor network and archives historical data of the Tor ecosystem. In most cases, whistleblowers have sensitive information about the government or a company. They can be easily traced and even prosecuted if they share the information on the surface web. SecureDrop is a site that protects the privacy of journalists and whistleblowers.
However, the dark web environment can be unpredictable and sometimes dangerous, filled with scam links, phishing sites, and other malicious threats. That is why we emphasize caution, vigilance, and adherence to best security practices when exploring these hidden corners of the internet. Dark.fail has become one of the most trusted alternatives to the traditional Hidden Wiki. This directory focuses on providing users with verified, frequently updated links to a broad range of dark web services, including marketplaces, forums, and whistleblower platforms.
Top Dark Web And Deep Web Forums To Monitor Today – Detailed List
It’s a cornerstone of transparency and investigative reporting on the dark web. To explore dark web sites that are safe in 2025, combine the right tools with smart browsing habits. Verified directories, anonymity tools, and cautious clicking make all the difference.
Use Active Monitoring Of Financial And Identity Theft
Depending on your preference, you can find links in well-categorized groups. These categories include email providers, news sites, privacy, and commercial services. The deep web is the part of the internet you can’t access through search engines like Google and Bing. Also referred to as “non-indexed” content, it’s any content hidden behind some kind of access control such as a log-in or code word.
Can WiFi Owners See Your Internet History?
This added layer of security keeps your identity hidden and shields you from online threats. The Hidden Wiki has long been one of the most recognizable entry points into the dark web. It began as a simple, categorized directory of .onion links — helping new users find forums, search engines, whistleblowing tools, and more. Back when reliable dark web search engines were limited, the Hidden Wiki served as a trusted compass for exploring the hidden layers of the internet. Dark web search engines help users discover hidden .onion content that isn’t indexed by traditional search tools.
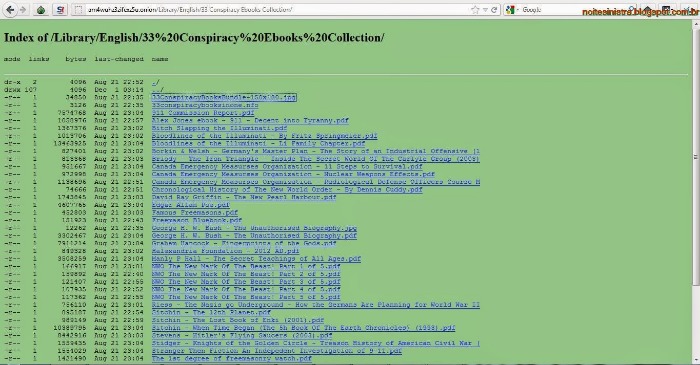
The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods. These platforms sell everything from drugs and fake IDs to weapons and hacking tools, resembling a digital black-market bazaar. Simply put, onion sites are websites that are hosted on the Tor darknet that use the “.onion” top-level domain instead of “.com,” or “.gov” for example. All Onion sites use The Onion Router (Tor) protocol to encrypt the user’s connections. It’s only possible to access onion sites through the Tor browser or by setting up some special network configurations. Swiss based ProtonMail is an encrypted email service that is quite popular with the cryptocurrency community.

Pro Tip: Use A VPN To Stay Safe When Using The Dark Web Search Engines
This platform’s library of websites currently totals 50, which may not sound impressive until you consider that all the links are active and popular. It’s a hidden collective of sites that you could only access through a special browser. Since all activity on the dark web is anonymous by default, it is definitely where the murkiest transactions on the internet take place. A study by researchers at King’s College London that examined the contents of over 2,700 darknet sites found that approximately 60% of them hosted illicit content. You can’t access these .onion sites from your normal web browser like the one you’re probably viewing this page on.
Stay Away From Questionable Sites
While people and organizations do host legitimate and useful sites on the dark web, it’s still best to tread cautiously. Despite Tor’s privacy-focused design, malicious entities are more likely to target your data in transit and on .onion sites. Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too.
- Using link verification tools or services that scan .onion sites for known malware or phishing attempts can also reduce risk.
- And then there’s malware—click the wrong link or download the wrong file, and your device could get infected.
- While it’s not 100% foolproof (no directory is), the Hidden Wiki helps minimize risks and provides a safer entry point for users who are new to the Tor network.
- To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web.
- You can’t access these .onion sites from your normal web browser like the one you’re probably viewing this page on.
Dark Web Links: The Best onion And Tor Sites In 2025
Without the right precautions, your IP address could be exposed, leaving you vulnerable to hacking, tracking, or even identity theft. The dark web is just a part of the internet where users can communicate and browse privately, often beyond the reach of standard government monitoring. In fact, you can even find many government and corporate websites on the dark web. Yes, governments can still monitor onion sites if they really want to. Local offices frequently monitor suspicious activities that involve their jurisdictions, so authorities might be closer to your anonymous communication than you know. Insights like these help researchers and advocates understand how and why Tor is being used.
Viruses, ransomware, and other types of malware are more common on onion sites than on the normal internet. Many pages have poor encryption standards and no other protections, so simply visiting a Tor site can infect your device. No, black market websites operate illegally and pose high risks of scams, fraud, and law enforcement action.
The Wasabi Wallet is a Bitcoin wallet that uses CoinJoin mixing to obfuscate transaction trails, enhancing user anonymity. BitBlender provides a mixing service that pools multiple users’ coins to anonymize their origins and destinations. EscrowBay offers escrow services tailored to dark web transactions, holding funds securely until both buyer and seller confirm satisfaction, reducing fraud. Together, these tools facilitate safer, more private financial exchanges essential for dark web commerce. Users turn to the Hidden Wiki because it simplifies navigation through the complex and often confusing dark web. Many people seek it out for privacy and anonymity, as the Tor network and the Hidden Wiki help mask identities and activities from surveillance.
Using Tails OS can further security, as all your data is reset every time you close the device. Alt Address provides disposable email addresses specifically designed for dark web use. This service helps protect your primary email when signing up for .onion services. I found it especially useful for testing new services without risking my main email address, though messages expire after 24 hours. Dark web surveillance involves monitoring information on the darknet, such as to identify compromised credentials being sold, or to track forums to anticipate (and prevent) cyberattacks. While it has legitimate uses, it’s also a hub for cybercriminals, hackers, and other threat actors.


