“You usually notice when you’re crossing the line into illegality. The biggest risk is unwittingly downloading something onto your computer, like images or hacking software,” he warns. It’s also important to note that your activities on the dark web aren’t completely immune to web tracking, and the expectation of anonymity can create a false sense of security. You can run a dark web scan to see if any of your data has leaked onto the black market. And if you think you’ve fallen victim to identity theft or fraud, be sure to report the internet scam just like you would any other crime.
Top 10 Dark Web Sites You Must Visit In 2025

A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want. A virtual private network (VPN) is a good way to mask Tor activities. It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor. The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. It will encrypt your traffic and data so no one can intercept it.
Hundreds Nabbed In Global Crackdown On Dark-web Drug Marketplace
Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons. With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential. It is a good way to prevent third parties from tracking online activities. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. Whereas the deep web is the part of the web not searchable by traditional search engines and requires special tools to access it. Also, you must log in or have a specific IP address or URL to access the deep web content.
- In this article, we’ll explain how these markets work, how you can keep up with changes in the darknet markets world.
- The second category consists of data stores, which specialize in stolen information.
- The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s.
- Besides monitoring and improving the network, the data can be used to detect possible censorship or attacks.
- The website has an advanced search filter and an easy-to-use interface, which makes it easy to find what someone is looking for.
- After more than a year of no updates, the site admin shut it down, reasoning that he couldn’t keep the list of onion links up-to-date.
Efficient Drug Trade On Darknet Markets
Note that data for 2020 only included data from January to March; price per gram is in US $. In this way, we collected 7100 promotion posts and 6408 review posts from forum posts in total. The agency, based in The Hague, built intelligence based on evidence from Germany, which it said seized the marketplace’s “criminal infrastructure” in December 2021. Most of the arrests were made in the U.S., which is in the grips of an overdose crisis. Synthetic opioids, mostly fentanyl, kill more Americans every year than died in the Vietnam, Iraq and Afghanistan wars combined.
A random dark web link can lead you to malicious software, phishing sites, and illegal content. Viruses, ransomware, and other types of malware are more common on onion sites than on the normal internet. Many pages have poor encryption standards and no other protections, so simply visiting a Tor site can infect your device. Behrouz Parsarad (Parsarad), residing in Iran, was the sole administrator of Nemesis. In this capacity, Parsarad established Nemesis and held full control over the marketplace and its virtual currency wallets.
- Tor browsers create encrypted entry points and pathways for the user, so dark web activity remains anonymous.
- These markets are dangerous anyway and shouldn’t be accessed even if they’ve onion addresses.
- Before clicking any of the dark web links below, you’ll need to get the Tor Browser (also called the Onion Browser) or another service that provides dark web access, such as the Brave browser.
- Articles from Journal of Medical Internet Research are provided here courtesy of JMIR Publications Inc.
- Despite Telegram’s anonymity, the dark web is still a hot spot for illegal trading of malware, illicit goods, and stolen data (such as stolen credit card information).
Are Onion Sites Safe?
Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found. Onion sites are “crawled” and added to the list provided their “robots.txt” file permits it, and if it is not on their blacklist of sites with abuse material. Site operators can also submit their own .onion sites for indexing.

Can You Be Traced On Tor?
Hence, it should be the top priority to track these platforms and shut them down as quickly as possible. Just like on the regular internet, phishing is a big problem on the dark web as well. Fraudsters create fake versions of popular darknet sites to trick users into entering login details or personal data. If you fall for it and log in, they immediately steal your credentials and either sell or use them for other scams.
The Legality Of Accessing The Dark Web
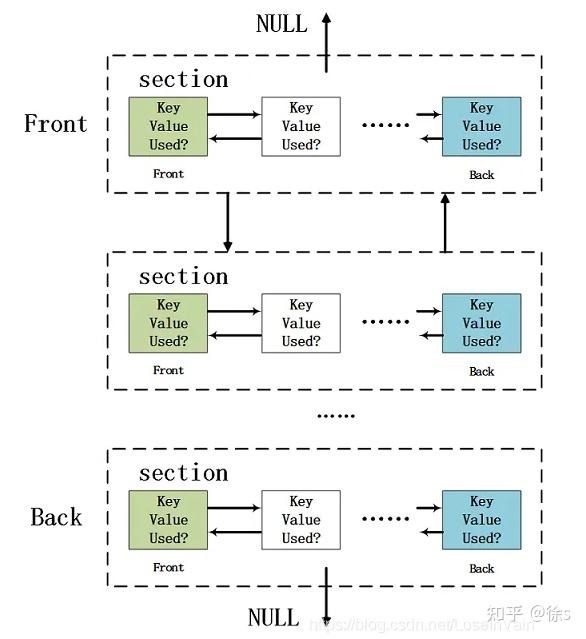
When you use the Tor network, your traffic is layered in encryption and routed via a random relay, where it’s wrapped in another layer of encryption. As a result of the action, the platform’s infrastructure in the Netherlands was taken offline and its administrator – a 30-year-old German national – was arrested in Barcelona, Spain. In parallel, measures were taken in Germany and Sweden against one moderator and six of the marketplace’s highest vendors, and assets worth €7.8 million seized.
(He declined to share detailed numbers, which he says are part of a still-unpublished study.) “What happened in 2017 was very unique, that one-two punch,” Christin says. “But that doesn’t seem to have dented the ecosystem in a major way.” “History has taught us that this ecosystem is very, very resilient,” Christin says. “It’s part of a cycle, and we’re in the chaotic part of the cycle. We’ll have to see how it recovers. But if I were a betting person I would put more money on it recovering than on it dramatically changing.”

How Much Is Stolen Data Sold For On Darknet Markets?
Valued at approximately $15 million, Abacus Market is one of the most lucrative platforms in the dark web ecosystem. In some cases, established sellers on closed-down markets are welcomed onto new markets as digital “refugees” and have joining fees waived. Last week, one of the dark web’s most prominent drug marketplaces – Archetyp – was shut down in an international, multi-agency law enforcement operation following years of investigations. It was touted as a major policing win and was accompanied by a slick cyberpunk-themed video. Clicking on random onion links is quite risky and isn’t recommended.
Email Services
These platforms, accessible via Tor, offer anonymity and reliability. Popular darknet market lists and links help users navigate the best options, ensuring access to verified darknet sites and marketplaces. The darknet drug market continues to grow, with 2025 projections indicating expanded availability and improved user experience. Darknet magazines and forums provide updates on new markets, onion addresses, and URLs, facilitating seamless transactions. Cryptomarkets on the darknet remain a key resource for those seeking privacy and efficiency in online trade.
Digital products, such as e-books, software, and online courses, also play a significant role in the ecosystem, catering to a diverse audience. These advancements will further solidify their position as a secure and reliable option for users worldwide. Pharmaceuticals and recreational drugs remain the most sought-after products on these platforms, with vendors offering a wide range of high-quality substances.
The homepage reminds users to disable JavaScript, use reputable VPNs, and always access .onion services through the Tor Browser. This safety-first approach has earned it a reputation as a reliable starting point for dark web exploration, especially among journalists, researchers, and privacy advocates. You can use dark web monitoring tools, such as NordVPN’s Dark Web Monitor, to check if your data has been leaked.