Those who access the dark web do so via the Tor (The Onion Router) browser. So, that means that the number of pages increased by over 100 trillion in just over three years. Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine). So, even though it does exist on the internet, Google doesn’t index any of these pages or content.
Marketing
You’ll also enjoy its Smart DNS support, 24/7 live chat service, the Keys password manager, and a lot more. Feel free to grab its 49% discount thanks to 3 free months for the annual plan. We love it because of its simplicity, which, as you saw, lets you visit the dark web in seconds.
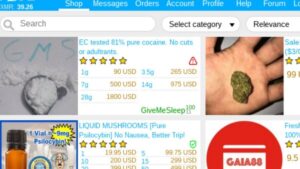
- If you think the Dark web marketplaces are just online shops, you’re wrong — these sites are the actual weapon stores for criminals.
- Unfortunately, some oppressive regimes have figured out a way to block Tor traffic.
- Facebook is aware of attempts by many governments to restrict access to a tool that allows strangers across the web to talk and collaborate freely.
- Like any other site of such nature, Awazon Market isn’t free from risks, so be careful while accessing it.
|}
However, due to copyright infringement, Sci-Hub is considered illegal and banned in many countries. Pastebins are text sharing services, useful for sending and sharing large snippets of code or text. ZeroBin offers an extra secure version of this service by only encrypting and decrypting text in the browser, meaning their servers have no knowledge of what is passing through it. Onion sites (aka Tor sites) are websites only accessible on the dark web; you can’t view them using a regular browser. Their URLs (aka dark web links) have .onion as the domain, instead of the common surface web domains like .com or .net. Viewed from the destination, the traffic appears to originate at the Tor exit node.
A look with the Tor browser at a darknet directory such as the uncensored Hidden Wiki reveals that seemingly anything goes on the darknet. We may earn a commission when you buy through links on our sites.©2025 GIZMODO USA LLC. The Tor Browser’s interface is based on Mozilla Firefox, so it’s very similar in features and look. However, it doesn’t allow you to sync between various devices, as that could be a security and privacy hazard. You can install extensions, but it’s not advised, and you better thoroughly check the developer behind every plugin. You can download the Tor Browser on Windows, macOS, and Linux desktop computers, as well as on smartphones and tablets based on Android.
Did The Silk Road Marketplace Go Under?
Understanding the Dark Web and its access tools, such as Tor, is crucial for anyone considering exploring these hidden parts of the internet safely and responsibly. Using Tor is especially helpful in countries where authoritarian governments censor the internet, preventing citizens from accessing news outside their country. These URLs are usually very long, consisting of a random jumble of letters and numbers. Though you likely won’t remember the addresses of onion websites, you can find these URLs on various websites on the internet. Unlike Ahmia and Haystak, however, DuckDuckGo doesn’t search .onion sites.

Do I Need A VPN To Access The Dark Web Using Tor?
Many dark web search engines are available, and no single option is objectively the best. While the best dark web sites listed above are a good starting point for a safe, legal surfing experience on Tor, there really is no substitute for a VPN. Many dark web links could get you mixed up in some kind of criminal activity of another, whether you’re looking for it or not. The deep web is rife with sales of illicit drugs, weapons, and goodness knows what else, and steering clear of these nefarious web pages is easier said than done. ZeroBin is a minimalist paste-bin tool that allows users to share text securely and privately on the Tor network. With onion sites like Wikipedia, you can continue learning and gathering information on a wealth of issues, even in places where the standard Wikipedia is restricted or censored.
Use Secure Communications
Don’t click on suspicious links, be skeptical of what you read, and avoid dark web marketplaces if you don’t want to stumble on illegal activity or content. Onion sites are considered part of the deep web because search engines like Google and Bing can’t index them. Such cybercrime is part of the dark web, facilitated via the darknet, which is a very small part of the Internet that is not visible to search engines and ordinary Web browsers. Another common method for finding onion services is through onion directories or link lists, which are essentially curated lists of .onion addresses categorized by topic.

How To Turn Off SafeSearch On Google, Bing, DuckDuckGo, Yahoo
The dark web is a murky part of the internet that isn’t accessible via a normal browser — and can be dangerous to visit if you don’t know what you’re doing. We’ll show you how to access and browse dark web sites, and how using a VPN to encrypt your connection can help you visit the dark web more securely. One common reason .onion sites go offline is due to Distributed Denial-of-Service (DDoS) attacks. These attacks overwhelm servers by flooding them with massive amounts of fake traffic, making legitimate access nearly impossible. Since many dark web platforms lack the sophisticated resources needed to defend against such large-scale disruptions, affected .onion sites can remain offline for extended periods. The entry node encrypts your traffic and it bounces across several nodes in the Tor networks until it reaches the exit node.
What’s The Difference Between Tor And VPN?
Anonymization services prevent your own internet activities from being spied on. What we see and use on the internet in web browsers such as Edge, Chrome, Firefox, Opera, and Safari is only a fraction of what is actually available. Information and data can be published and exchanged with the greatest possible anonymity on the so-called darknet, as PCWorld first noted in 2013.
- Anonymity of the dark web is one of the main draws for using onion sites, and most dark web links use a “.onion” domain.
- It’s important to arm yourself with a good VPN (Virtual Private Network) when you want to enter the dark web to protect your privacy and anonymity.
- The dark web and the deep web are often used interchangeably, but they’re two distinct concepts.
- Go to the security settings and set the security level to “Safest” to minimize potential vulnerabilities.
- Navigating the dark web often begins with accessing .onion links—specialized web addresses accessible only through the Tor network, designed to provide enhanced privacy and anonymity online.
The Marketplace As An Arsenal
This provider’s performance is top-tier, with full Tor Over VPN support to make things simpler. Connect to ANY of its 3,000+ servers, open Tor, and do your magic! ExpressVPN’s intuitive apps work on up to 8 devices at a time, ensuring protection for the entire family. It also has 10 simultaneous connections, support for all devices, and server obfuscation that works in China. You’ll appreciate its added features, such as Threat Protection, which shields you from malware and trackers. NordVPN also includes Double VPN servers to double your encryption and make you untraceable.
Opera is another great choice, and it’s known for the robust features it offers for free. When it comes to privacy, there’s a built-in VPN service that hides your IP and encrypts your traffic, and you don’t need to pay for it unless you want to upgrade to a pro version. On top of that, Opera blocks all ads before the website even loads by default. There are also other features that include their tool for saving battery usage, integration with various social media and instant messaging platforms, and their AI assistant called Aria.

Tor volunteers face legal inquiries as illicit materials can pass through their relays without their knowledge. Authorities have confiscated volunteers’ computers, though privacy advocates defend them. Using the Tor browser is simple, but knowing when to fire it up is more complicated.
What Is WPA2 (Wireless Protected Access ?
It can route data to and from onion services, even those hosted behind firewalls or network address translators (NAT), while preserving the anonymity of both parties. Tor is necessary to access these onion services.59 Because the connection never leaves the Tor network, and is handled by the Tor application on both ends, the connection is always end-to-end encrypted. Despite the anonymity features of Tor Browser, users should also be aware of the potential for surveillance and tracking. While Tor makes it significantly harder to trace online activities, it does not guarantee complete anonymity. Internet service providers may also be suspicious of Tor usage and might monitor traffic patterns, even if they cannot see the content of the encrypted communications.