To protect your data from the websites you visit, one of the most effective steps is to hide your IP address, which can reveal your location, identity, and browsing habits. Using a virtual private network (VPN) masks your real IP by routing your internet traffic through a secure server, making it appear as though you’re browsing from a different location. A VPN also encrypts your connection, keeping your data safe from surveillance and unauthorized access.
What Are EWallets And How Safe Are They?
The entry node is the first server in the Tor chain, the relay node is the middle node and the exit node is the last server in the network. The internet is huge—even in its shadows—it is possible to wander legally there. By distributing communication over several nodes, it obscures the user’s IP address. The inherent advantage of unindexed content becomes apparent in the preservation of privacy. Protect your business with end-to-end encryption and compliance-ready security. Using Forest VPN enhances your privacy by encrypting your data, making it unreadable to outsiders, and providing an additional layer of security against potential threats on the dark web.
- SecureDrop uses Tor to provide a safe way for whistleblowers to contact various news outlets.
- Unfortunately, it’s also a place where the bad guys can offer their services – for example, hackers or hitmen.
- By selecting trusted search engines, crafting precise search queries, and diligently verifying sites, you can greatly enhance your safety and effectiveness.
- After installation, verify the file’s authenticity using PGP – the instructions are on Tor’s website.
- This browser is the most suitable option for accessing the dark web, thanks to its multiple layers of encryption.
This is especially important for individuals in regions where press freedom is restricted or where government surveillance poses risks to journalists and activists. DuckDuckGo is a reputable US-based software company, so their Tor site itself is safe to use. That said, you still might get malicious links in your search results, so you still need to proceed with caution with any page DuckDuckGo takes you to. Sections of the dark web are often closed down too, as part of police operations. Open up Tor, and you won’t suddenly see the dark web staring back at you.
How To Stay Safe On The Dark Web
Each one offers unique features, such as better privacy and extensive .onion site indexing. The so-called “Dark Web” often conjures up images of hidden bazaars for illicit goods, secretive communication channels, and shadowy corners of the internet inaccessible through standard search engines. While the deep and dark web provide valuable platforms for privacy and access to restricted information, they also harbor significant risks. Among the most pressing concerns is the prevalence of illegal activities, such as marketplaces for illicit goods, fraudulent services, and even cybercrime networks. Engaging with such content can lead to severe legal consequences, and the anonymity offered by these layers often attracts malicious actors, posing threats to unsuspecting users.
Social Media
The site isn’t dormant; you can still find some of their old and very interesting blog entries and helpful resources. Info like your name or email address never needs to be shared on the dark web. You should also limit the number of financial transactions you make on Tor banking portals. This space for private free speech also carries the risk of exposing you to harmful content. Hidden Answers is one of the biggest question-and-answer dark web sites. This makes Riseup a vital tool for people in oppressive environments or anyone concerned with online privacy.
How To Set Up And Use The Tor Browser To Search onion Sites

With the above dangers, it’s imperative to tread carefully as you step into the dark web. Radar Rundown Ad blockers are the best protection against disruptive ads. While they might sound the same, these websites are fundamentally different. Read about the adventures of modern-day explorers who have made it their mission to venture into the tunnel network of huge American universities. The site is different from our whole list, but still worth a mention. Still, while the latter has a large digital collection of comic books, the Imperial Library has a large collection of books.
Using Onion Over VPN — All You Need To Know

Despite being under legal scrutiny, Cracked.io remains one of the key hubs for those involved in cybercrime activities. RAMP enforces extremely strict access policies, with one key requirement being a solid reputation on other well-known forums like XSS or Exploit.in. In other words, if you don’t already have a credible track record, don’t even bother knocking.
- The content of all these pages is stored on Google’s servers, but it’s mostly outdated, old content; smartphone app content; journals; court records; private social media profiles, and much more.
- It uses dedicated IP addresses, enabling you to access IP-restricted networks.
- Typically, when people talk about the “dark web”, they almost always mean Tor websites.
- Despite multiple attempts to break Tor (some of which have had some partial success), it remains by far the best way to achieve true anonymity on the internet.
- If there has ever been a time when you wanted to look at a backlog of the world’s historical newspapers, Elephind is for you.
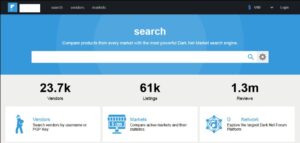
StartPage – User-Friendly Dark Web Search Engine Like Google

This includes military-grade 256-bit encryption reinforced with a 2048-bit DH key and SHA2-384 authentication to ensure your traffic arrives at its destination safely. This adds extra protection since opening Tor itself encrypts your traffic. We recommend you only visit safe dark web links to explore such as The CIA, Facebook, DuckDuckGo, and Torch. While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity. That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy.
If you loved Elephind and want an alternative, you’ll be happy to know that all of its library is still accessible via Veridian’s website. Not everything on the web will show up in a list of search results on Google or Bing; there are numerous places that the sites’ web crawlers cannot access. OnionName lets you generate an .onion domain name that starts with a specific keyword — like onionamev33r7w4zckyttobq3vrt725iuyr6xessihxifhxrhupixqad.onion/, which is OnionName’s dark web link. The keyword in that example is “onioname,” which is right at the start of the .onion link.

Dark Web Tools And Services
DuckDuckGo is one of the leading private internet search engines on the open web. It doesn’t track your browsing history, location, or any other data. It’s so secure and privacy-oriented that the Tor browser uses it as the default search engine. Proton Mail’s dark web version provides end-to-end encrypted email with enhanced privacy protection. The service doesn’t require personal information to create an account and works seamlessly through Tor.
User Intent
Fortunately, you can’t just stumble onto dark web websites by accident. No, it isn’t illegal to browse the dark web, and there’s nothing inherently wrong with visiting a Tor website. Enable MFA wherever possible to protect your accounts from unauthorized access.

Never log in with your real name or reuse passwords from other accounts. Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info. If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address. Some are looking for illegal stuff they can’t buy elsewhere, like drugs or counterfeit documents. These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information.
Over time, Blockchain.com expanded its offerings to include a digital wallet service, which has become one of its most popular features. This wallet service emphasizes security and privacy, with advanced measures in place to protect users’ funds while providing them with full control over their private keys. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. Many people see hacked information and stolen card data being sold on the dark web.