These differences aren’t necessarily clear-cut, as there are overlapping aspects between the Deep and Dark Web. Therefore, it’s likely that not all deep- and dark-web file repositories represent good intentions. Accessing and using Dark Web protocols such as Tor is not illegal; it’s just been adopted as the platform of choice by many bad actors who undertake illegal activities. The firm faced over $50,000 in fraudulent transactions and legal costs. Additionally, clients, unsure of the firm’s ability to secure their data, began terminating contracts, resulting in a 20% revenue loss over six months. The breach also exposed operational vulnerabilities, as the company’s incident response plan proved inadequate to contain the attack.
- Of course, this comes with its own dangers as we never know if the dead drop is being monitored.
- The dark web is the portion of the internet that is not indexed by traditional search engines such as Google or Bing.
- However, remember that there are risks involved, and engaging in any illegal activities or purchasing illicit goods is both unethical and illegal.
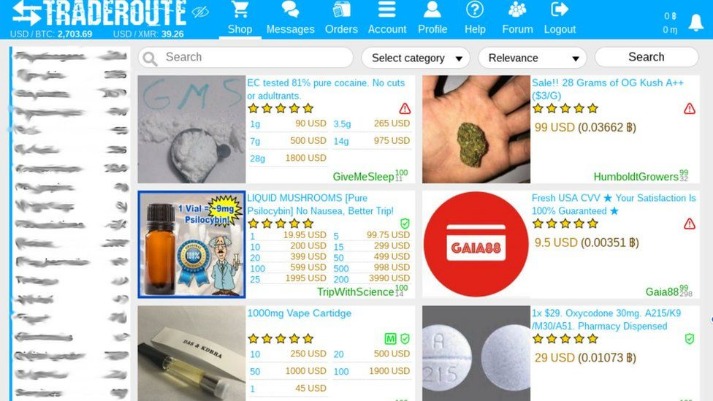
- The marketplace has a simple interface, lets users filter logs easily, and accepts Bitcoin, Monero, and Litecoin for payments.
- Similarly, single vendor shop revenue fell concurrently with the recovery of traditional darknet markets from around June through end of year.
Accessing DNMs
Server admins will have to either make special agreements to get initial sellers on board, or supply products themselves to get things started. I do not condone the use of DNMs to purchase or sell drugs and other illegal materials online. DNMs are inherently dangerous places and its users risk losing their money, their freedom, and their lives.Are you suffering from drug addiction? Torzon Market has established itself as a significant player in the darknet ecosystem, offering a secure, user-centric platform for anonymous trading. Its commitment to privacy, diverse product offerings, and robust security measures make it a preferred choice for users seeking discreet transactions within the darknet.
The cost can be exorbitant, but for victims, it’s always higher and devastating. For instance, stolen data can result in unauthorized payments, the draining of accounts, or even registered loans. The sad reality is the fact that law enforcement agencies can’t track and prosecute perpetrators or even take down such content given the anonymous nature of the dark web.
What Is Bitcoin?
This unique infrastructure fosters an environment for illegal commerce, posing significant cybersecurity risks for businesses. These markets exist on the Tor network in order to create security and anonymity for both users and darknet providers. Transactions take place via a cryptocurrency like Bitcoin using dark wallets to protect the seller and buyer. The payment is held in escrow by the site operator to discourage scammers. The only exposed link in the chain is the actual shipping of the goods through the postal system. Darknet or dark web marketplaces are a hidden part of the internet that surface web users can’t access; they can only be accessed with special anonymity software called Tor.
Throughout 2022, we observed a negative relationship between funds sent to regular darknet markets and those sent to single vendor shops. For instance, we see single vendor shop revenue spike beginning around March, around the same time traditional darknet market revenue began to fall. Similarly, single vendor shop revenue fell concurrently with the recovery of traditional darknet markets from around June through end of year. Four of the top five highest-earning darknet markets in 2022 were conventional, drug-focused darknet markets, while just one, Brian Dumps, was a fraud shop.
Microsoft Strengthens Security After China-Linked Attacks
You can use a dark web scan tool to tell if your data has landed on the dark web. The tool scans the dark web marketplaces and forums for signs of compromised personal credentials. That’s exactly what happens when it comes to the dark web marketplaces. We understand the curiosity to venture into the dark web, but you also need to understand that it’s never safe to venture into this portion of the internet without fully understanding what it entails.
Best Privacy Protection Apps For Ultimate Anonymity And Security
He’s heard too many stories about buyers getting busted when law enforcement organizations take over sites to feel comfortable. After weathering seven in-person busts over the years, he’d prefer not to get caught again. This article should help you understand what darknet markets are, the dangers they pose, and how to protect yourself. While it’s interesting to explore the darker parts of the internet, dark web marketplaces present very real dangers to users.
What Is A Dark Web Alert? A Guide For Businesses
When one goes down, two more emerge with new ideas, better technology, and greater difficulty to track. It’s an ever-evolving ecosystem—constantly shifting, reinventing itself, and adapting. Ethically, they must minimize harm, responsibly handle any stolen or sensitive data (often notifying victims or law enforcement), avoid entrapment, and maintain research integrity. Last September, another international police sting, Operation DisrupTor, announced the results of a push to catch drug dealers and other criminals who had used Wall Street Market. A hundred and seventy-nine people were arrested in seven countries, a hundred and twenty-one of them in the U.S.
Easy Steps To Access Dark Web On Your Phone Safely In 2024
But somewhere between production and purchasing, things can get dirty. For example, an insider or factory employee might quietly slip away with an unmarked gun and sell it online. Once it lands on a darknet marketplace, it becomes part of the illegal weapons trade. While this market started in Canada in 2021, WeTheNorth now sells to both Canadian and international users.
Is It Illegal To Access The Dark Web?
Tor establishes a secure network circuit for each browser session, which connects Tor nodes deployed around the world at random. These nodes encrypt your browser traffic in layers at each node hop on its way to/from the source (your browser) and the destination (a hosted hidden service). Established in 2022, WizardShop is one of the biggest data stores on the dark web, focusing mainly on carding and financial data. STYX Market focuses specifically on financial fraud, making it a go-to destination for cybercriminals engaged in this activity. Yes, you can buy CP or child pornography along with other pornographic materials.

For example, non-compliance can result in fines of up to 4% of an organization’s global annual revenue. Navigating dark web marketplace links can be risky; however, with the right tools, you can explore safely. These platforms have short lifespans due to law enforcement closures or frequent domain address changes.
As law enforcement agencies continue to grapple with the challenges posed by Torzon, its prominence as one of the best dark web marketplaces remains a cause for vigilance and monitoring. As per our data provider, around 20 prominent marketplaces are active, alongside several smaller ones on the deep web. Dive into the world of the dark web as security professionals share their concerns about the top 5 dark web marketplaces. Explore the potential security features that these hidden marketplaces bear. Why are these markets still seen as enticing places to sell drugs, despite the risks?
Xennt, who had a lifelong fascination with underground fortresses, lived in the bunker. Inside the bunker, Xennt’s team installed servers that hosted dark-Web sites trading illicit products and images, including terrorist material and images of child abuse. This usually involves providing an email address and a username, as well as setting up a password. Make sure to choose a strong password and keep your login details safe.
Visit CyberNod and take the first step toward a secure digital future. A multi-layered cybersecurity strategy incorporating Dark Web monitoring, cybersecurity risk assessments, and employee training can significantly reduce vulnerabilities. Corporate espionage is a growing concern, with competitors and nation-state actors leveraging stolen data to gain unauthorized access to intellectual property, trade secrets, and financial records.



