Whether local or international goods, research documents, banned drugs, you name it, everything is available on this dark web platform (that’s one of the reasons why this should be monitored for security purposes). Unlike other search engines, it does not collect or share web activities and personal data of users. Monitoring the activity on these platforms is crucial for fraud detection, brand protection, and financial intelligence.
How Fake IDs And Documents Are Purchased On The Dark Web
- It also keeps the graphical copy and text of the page for better accuracy.
- HSI New York leads and directs all operational and administrative activities of the El Dorado Task Force (EDTF).
- While some cryptocurrencies, such as Monero, are more challenging to trace due to enhanced privacy features, law enforcement agencies continuously develop methods to uncover the financial trails left by criminal actors.
- Many social media platforms keep their presence on the dark web, and it is no surprise that Facebook has a .onion portal.
- Ultimately, addressing fake document usage necessitates more than law enforcement—it requires broader societal reflection and moral education emphasizing integrity, accountability, and the importance of shared societal values.
- This .onion link makes it impossible for hackers to impersonate your profile.
It maintains a very strict level of user verification and integration with an official Telegram account to provide real-time updates to users. Various cryptocurrencies such as Bitcoin and Monero can be used to make purchases. Never log in with your real name or reuse passwords from other accounts. Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info.

History Of Dark Web Marketplaces
My friend produces counterfeit bills and sells them on the dark web worldwide, he gave me some but the problem is that they are euros, and I live in hong kong, how do I go about exchanging these into my local currency? Or if you have any other ideas of how to make good use of these in my country. After looking at all of the receipts, additional agencies were contacted because they indicated the counterfeit money was passed at many other locations. CRENSHAW CO., AL (WSFA) – Clerks at a Brantley store are being credited with helping stop a multi-state counterfeit money spending spree. It hosted over 7,000 .onion categorized links to make surfing the web easier.
As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. For this reason, you must watch out and avoid opening anything that looks suspicious to you. All in all, it is not illegal to access the dark web, but it can create issues for you. If you don’t take the necessary measures, many unsavory activities can expose you to unnecessary risks. Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed. Besides, victims of crime may want to hide their identities from their perpetrators.
What’s The Difference Between Deep Web & Dark Web?
The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s. A network browser gives you access to sites with the ‘.onion’ registry operator. Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship. It works by sending internet traffic through volunteer-operated nodes all over the world.
Appeals Court Finds Trump’s Tariffs Illegally Used Emergency Power, But Leaves Them In Place For Now
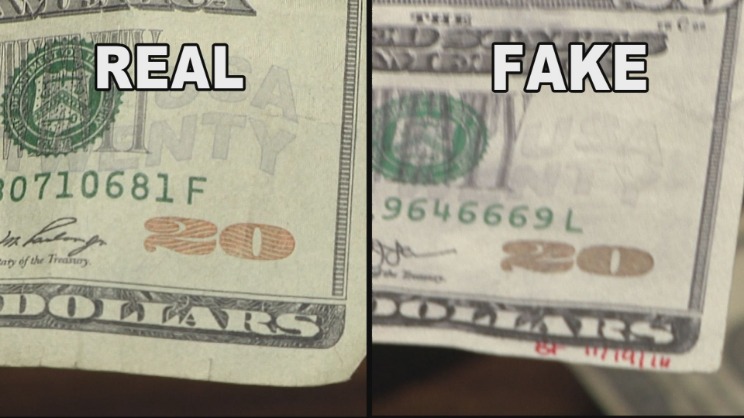
Today counterfeit U.S. bills are only a tiny fraction of currency in circulation. Even so, the Secret Service made more than 1,580 counterfeiting-related arrests last fiscal year, seizing $204 million in phony bills. A further analysis is invited which treats the counterfeit notes as part of an actor-network. In this perspective the discourse around it, the production and distribution system, is part of a set of practices that produce the product as a workable entity. In their discussion the buyers mentioned how they slipped the counterfeits into the supply chain.
Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. It is one of the most notorious credit card shops on the dark web. It has built a reputation for being a reliable source of stolen credit card data and PII. Renowned for its extensive inventory of financial data and sophisticated operating methods, Brian’s Club is a key player in the underground economy of financial cybercrime. With the growing threat from cybercriminals who sell stolen credit card information on the deep web and dark web, businesses need to stay ahead of the game. Over the years several advanced tools have been developed to help track and prevent such fraudulent activities.

Tracing Cryptocurrency Transactions
These sites provide the ransomware operators with a platform to accept payments from the victims, a space to shame them and apply pressure, and somewhere to leak their data if they don’t pay. The concept known today as the Dark Web set its foundation in the early 2000s. In March of 2000, Freenet was released to allow a censorship-resistant way to use the Web. It also opened the way for sharing illegal pornographic material and pirated data. One of the key tools used on the Dark Web today was first released in 2002 – Tor, The Onion Router. Users gain greater anonymity online when using Tor because it encrypts Internet traffic and passes through several nodes.
The price tag for these items may be surprising, with usernames and passwords selling anywhere from $.10 to $1 and fingerprints selling for about $2 each. The Deep Web contains all the web sites that web crawlers cannot index. Examples of sites on the Deep Web that require a login to access include bank accounts, Netflix accounts, and social media accounts.
Conclusion: The Real Risks And Why Fake IDs Are Never Worth It
David Allingham, 65, who was sentenced to 13 years in prison for his prescribing of opioids and amphetamines has been ordered to forfeit a $168,000 money judgement and two real… Sales had been carried out via private messages and other encrypted chat platforms in a further effort to hide the activity. The effort was a follow-up to an earlier operation, dubbed Deep Money, which had targeted the crime gang involved in making and distributing the fake currency.
Real-World Examples Of Significant Law Enforcement Operations

As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms. The dark web marketplaces are mainly defined into two categories. He explained to Elliott that he relied on cash because he was an investor in a marijuana business that was prohibited from using banks. The fakes — reproductions of $100 bills phased out in 2013 in favor of a harder-to-fake currency — had been printed on high-quality laser printers and specialty paper. The dark web’s backbone is a system called the Onion Router, known as Tor, a network of software and online connections that mask those who use it. Tor has attracted both criminal and legitimate users — political dissidents overseas, for example — seeking to avoid government surveillance.
Think of Tor as a regular browser like Firefox, Google, or Safari. The only difference is that it passes your traffic through random nodes before reaching the destination. This means your activities cannot be traced or your browser history exposed. There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale. Not every visitor is a criminal, but this is where most cybercrimes begin.
Although you can’t use just any browser, all that’s needed is downloading and installing a special browser like Tor. Users of the Dark Web will often use a VPN to hide their identity and location further, but accessing the Dark Web is not required. For in-depth insight on these research strategies, read this guide, as used by Bitsight analysts, to help enhance your threat intelligence program. With an option to buy funny money from Fake Money Forum, there’s no limit to what you can achieve.

The accessibility and perceived anonymity of the dark web make these transactions increasingly common, highlighting an escalating security challenge for law enforcement and government agencies worldwide. Dark web monitoring platforms, such as Lunar, provide an automated solution to safeguard personal identifiable information (PII) and credit card details. These platforms continuously scour the deep and dark web, looking for any traces of your sensitive information. By setting up alerts, businesses can receive notifications whenever their PII or credit card information appears in suspicious contexts. This proactive monitoring enables businesses to track and investigate potential threats in real-time, helping to prevent fraud before it can impact their operations. The use of such platforms is crucial for maintaining the integrity and security of customer data, and it provides an additional layer of defense against cybercriminal activities.



