Archetyp Market was dismantled in June 2025 during Operation Deep Sentinel in a coordinated raid across six countries. At the time, it had over 600,000 users, 17,000 listings, and approximately €250 million in transactions. Authorities seized €7.8 million and arrested operators in Germany, Spain, Sweden, Romania, the Netherlands, and the US Europol leads takedown of Archetyp. Russian Market has operated since 2019, specialising in stolen credentials, stealer logs, and remote desktop access. Threat reports consistently rank it among the top ten darknet sites Top 10 Dark Web Markets.
As a result, consumers need to be vigilant about protecting their credit card information and take necessary precautions to avoid falling victim to these scams. Chainalysis data shows darknet marketplace revenue dropped post-Hydra seizure in 2022 but recovered to $2 billion in Bitcoin inflows during 2024 Darknet market BTC inflow drop and shift to Monero. Abacus alone represented nearly 5 per cent of total DNM revenue, underscoring the ongoing scale of underground commerce. The closures are unlikely to spell the end of darknet markets as new ones will no doubt emerge. When one goes down, two more emerge with new ideas, better technology, and greater difficulty to track. It’s an ever-evolving ecosystem—constantly shifting, reinventing itself, and adapting.
Countries With The Highest Number Of Indirect Tor Browser Connections In 2023
Additionally, consider using virtual credit cards or prepaid cards for online purchases, as they limit exposure to your personal credit card details. By choosing a secure payment method, you can significantly reduce the chances of your credit card information falling into the wrong hands. To protect yourself, it’s crucial to monitor your credit regularly, report any suspicious transactions promptly, and use secure payment methods online. Additionally, securing personal information and maintaining cautious online behavior can minimize the risk of falling prey to credit card fraud on the dark web. With this stolen information, fraudsters can make unauthorized purchases, withdraw funds, or even create counterfeit credit cards. The risks are real, as victims can face significant financial losses, damage to their credit scores, and potential identity theft.
- Law enforcement takedowns, such as Archetyp, demonstrate both impact and adversary adaptation.
- Authorities seized €7.8 million and arrested operators in Germany, Spain, Sweden, Romania, the Netherlands, and the US Europol leads takedown of Archetyp.
- By adding an extra layer of authentication, financial institutions reduce the risk of fraudulent activities during transactions.
- This new trend for marketplaces winding down in an orderly fashion is known as “sunsetting” or “voluntary retirement”.
- Some senior threat groups even provide tutorials and share their attacking procedures to the budding hackers.
The Significance Of This Data

To avoid such losses, it is crucial to regularly monitor credit card transactions, report any unauthorized charges promptly, and take proactive steps to protect personal information. They can suffer from financial loss, identity theft, and damaged credit scores. In some cases, consumers may not even be aware that they are victims of credit card fraud until they receive their monthly statement. Credit card fraud can also cause emotional distress, as consumers have to deal with the aftermath of the fraud, such as canceling their cards and disputing charges. Most of use just have the standard personal account, but Premier and Business accounts also exist, and are up for sale on the dark web. But those tiers don’t have much influence on dark web prices, which are largely governed by account balance.
Telegram Carding Groups
Given the explosive growth of these markets, organizations must prioritize proactive threat monitoring. Axis Intelligence provides dark web surveillance solutions that help businesses identify leaked credentials, fraud attempts, and malware risks before they escalate. On one hand, it offers privacy for whistleblowers, journalists, and citizens in oppressive countries. On the other hand, it’s notorious for enabling illegal activity, including drug sales, weapons trafficking, counterfeit ID trading, hacking services, and the exchange of stolen personal data. This can be stopped if law enforcement agencies can break any link, particularly dark web marketplaces, in the chain. Hence, it should be the top priority to track these platforms and shut them down as quickly as possible.
Cypher Marketplace
In this guide, learn about the benefits of common identity theft protection features and compare 12 identity theft protection companies. Not only is there a way for hackers to discover payment card numbers without breaking into a database, there’s also a booming underground black market for them. Around 65% of the cards for sale on the black market came from the U.S., which is no surprise given the credit card-centric culture and large population. Joker’s Stash was one of the largest and most infamous dark web carding marketplaces, operating from around 2014 until it voluntarily shut down in early 2021. It was known for selling high-quality stolen payment card details and used blockchain-based domains to evade law enforcement. The closure of Joker’s Stash left a gap in the cybercriminal ecosystem, which was later filled by other marketplaces.
Exploring Benefits And Risks Of Using Credit Cards Or Card
Carders tend to target specific sites that don’t have VBV or other protections against fraud. Some vendors even sell lists of “cardable” sites for a few dollars. For fledgling criminals who don’t know how to use stolen credit cards, there are plenty of free and paid tutorials for carding on the dark web. Payment Card Information Stolen or skimmed credit darknet market news card data (and the software to capture it) is a perennial bestseller. Aleksei Burkov, the owner of Cardplanet, operates carding websites on the Dark Web, is sentenced for nine-year for selling stolen credit.
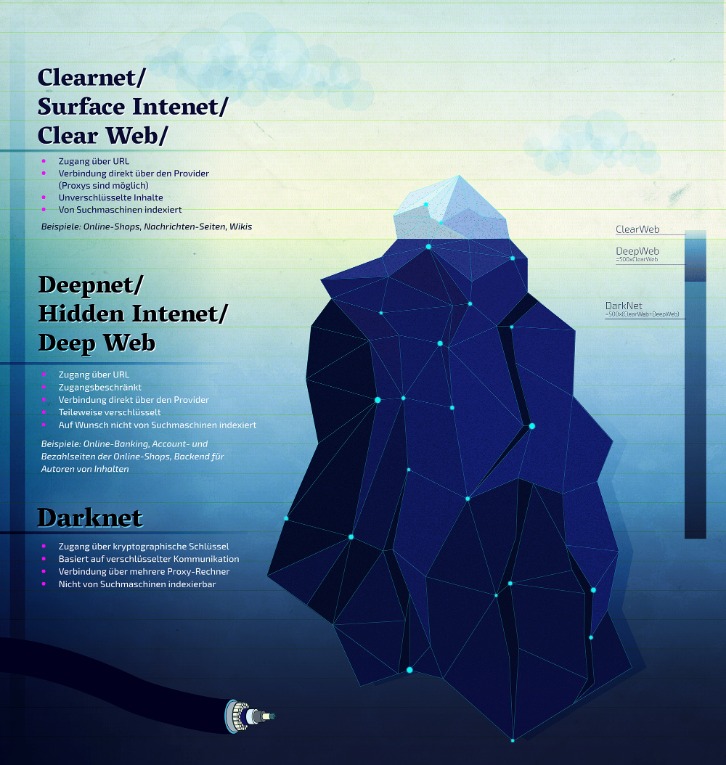
Founded in early 2023, shortly after major law enforcement operations shut down several competing platforms, Abacus quickly filled the void by prioritizing reliability, advanced security, and user anonymity. Ideal marketplaces support anonymous browsing through networks like Tor and I2P, utilize privacy-focused cryptocurrencies such as Monero, and implement measures to prevent tracking and transaction tracing. Platforms that provide clear guidelines for maintaining operational security (OpSec) and offer built-in tools for data obfuscation are especially favored. Dark-web marketplaces operate through encrypted networks, primarily utilizing anonymity-enhancing technologies such as Tor (The Onion Router) and I2P (Invisible Internet Project).

Cloned Credit Cards And Cardholder Data
Millions of credit card numberssome of which were apparently stolen from Sonic Drive-In restaurantsare now for sale on a dark web market. In October 2019, the firm found a database of darknet credit card market million credit and debit card records of mostly Indian banks’ customers uploaded to the Dark. What are your rights if your credit card or debit card information is stolen and unauthorized purchases or made.

How Much Is Stolen Data Sold For On Darknet Markets?
Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP. It is considered a go-to site for malware purchasing, providing keyloggers, trojans, and other Malware as a Service products. STYX Market focuses specifically on financial fraud, making it a go-to destination for cybercriminals engaged in this activity.

Curious About How Breachsense Can Help Your Organization Detect Credit Card Fraud? Book A Demo To Learn More
Over the years, carding has evolved from a simple process of skimming credit card information to a complex web of fraud and illicit activities. Carding has become a serious concern for financial institutions, law enforcement agencies, and consumers alike. The present-day form of carding has become more sophisticated, with fraudsters using various techniques to steal sensitive information from unsuspecting victims. Financial institutions can proactively strengthen their defences by integrating intelligence derived from FraudAction.
The stolen data supply chain begins with producers—hackers who exploit vulnerable systems and steal sensitive information such as credit card numbers, bank account information, and Social Security numbers. Next, the stolen data is advertised by wholesalers and distributors who sell the data. Finally, the data is purchased by consumers who use it to commit various forms of fraud, including fraudulent credit card transactions, identity theft, and phishing attacks. Be cautious when making online transactions, especially when it comes to sharing credit card information on the dark web. Carefully vet the websites and online platforms you use for purchases and ensure they have secure payment methods, such as encrypted connections and two-factor authentication. Look for reputable sellers with positive reviews and avoid suspicious websites or deals that seem too good to be true.
The U.S. has been trying to clamp down on illicit activity with crypto ties. Miklos founded Privacy Affairs in 2018 to provide cybersecurity and data privacy education to regular audiences by translating tech-heavy and “geeky” topics into easy-to-understand guides and tutorials. This not only helps protect your identity but also contributes to your overall cybersecurity in the digital age. However, if a hacker gains access to the unsecured network you are on, they can easily view your account details and steal or modify your information. One could end up with their details being used to open accounts on various pornographic websites or cryptocurrency trading sites.
FAQs About Dark Web Websites For Credit Cards
For example, an insider or factory employee might quietly slip away with an unmarked gun and sell it online. Once it lands on a darknet marketplace, it becomes part of the illegal weapons trade. As we mentioned earlier, not everything sold on dark web markets is illegal. As terrible as its reputation may be, some vendors sell legitimate goods or services. Some customers even use the dark web to make anonymous purchases, especially in areas where privacy is a huge concern. So, not everyone who shops there is looking for something illegal.



