
Vicy City is a new but popular marketplace on the dark web. The site allows users to find and buy a vast variety of products and services. It’s known for its strong security features (like a trusted escrow system, PGP two-factor authentication) and anonymity. Wondering if there’s an OG darknet market for financial crimes? Cybersecurity experts believe STYX is the one.
Monero Guide 2022
However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired. Tor establishes a secure network circuit for each browser session, which connects Tor nodes deployed around the world at random. These nodes encrypt your browser traffic in layers at each node hop on its way to/from the source (your browser) and the destination (a hosted hidden service). The Onion Router, or Tor, is a system routing internet traffic through a worldwide volunteer network of servers to conceal a user’s location and usage from surveillance or traffic analysis. This network facilitates anonymous communication.
Primary Risks For Users Of Darknet Marketplaces

To carry out your transactions, you can turn to an open-source graphical user interface (GUI) wallet developed by the community of Monero enthusiasts. In the evolving landscape of cryptocurrency, Bitcoin mixers represent a crucial tool for those prioritizing privacy. They symbolize the ongoing struggle between transparency and anonymity in the digital age, providing a means for users to navigate this complex and ever-changing terrain.
What Exactly Is Sold On These Marketplaces?
- Shut down in 2017 due to law enforcement action.
- Its robust security measures, such as private DNS servers and regular third-party audits, make it a reliable choice for navigating the dark web 3.
- These days, it lists over 11,600 illegal items, including hard drugs, hacking tools, and all kinds of cybercrime services.
- As one of PrivacySavvy’s resident VPN experts, he guides readers on protecting their online information and anonymity.
- A full guide to using Darknet markets to buy some stuff.
But, like all things in the underworld, it didn’t last. If for any reason, you decide to visit these hidden corners of the web, ensure you at least study and understand the common traps. Getting familiar with the tactics scammers use will go a long way in helping you protect your online data and assets. Too-good-to-be-true investment offers are another classic scam on the dark web.
Dark Web Marketplaces In Nederland 2025: De Complete Gids
These days, dark web forum admins are stepping up their game. They’re tightening security and carefully screening anyone who wants to join. This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk. The more secretive and exclusive, the better. According to a recent trend, the dark marketplaces faced a decline in revenue.
Is It Safer To Buy Monero Directly Or To Buy Bitcoin And Convert It?
This is a very easy process and only takes a few steps to complete. 10.) Once you open the file you will find a large block of text. It’s the key you will add to your accounts, so people can use your key to encrypt the messages they send you.
Darknet Markets Online – Full Markets List
You only need to have crypto, and you’re good to go. On the dark web, you don’t need to be a technical expert to design ransomware, and that’s dangerous. Even people with little to no knowledge can buy ready-made ransomware and launch attacks on their victims. They then use it to blackmail users until they pay a ransom. While you could find all sorts of products on Silk Road, drug sales quickly became prevalent because of the profits it raked in. In fact, by 2013, a Guardian article revealed that about 70% of listings were drug-related.
- Mixer makes it possible to conceal the origin or destination of BTC.
- Legally, they are limited to observing publicly accessible areas using tools like the Tor browser, without engaging in unauthorized access or illegal transactions.
- Here’s a breakdown of how the leading VPN providers stack up in key areas for secure dark web access.
- Despite Telegram’s anonymity, the dark web is still a hot spot for illegal trading of malware, illicit goods, and stolen data (such as stolen credit card information).
- If you’d like to use it to exchange currencies, please feel free.
On the other hand, it’s notorious for enabling illegal activity, including drug sales, weapons trafficking, counterfeit ID trading, hacking services, and the exchange of stolen personal data. The majority of people on these markets use cryptocurrencies. Monero and Bitcoin are two of the most commonly used digital currencies on the dark web markets. Due to being the most popular and the oldest coin, Bitcoin is traceable. However, Monero, on the other hand, is untraceable and the most trusted payment method on these markets. Therefore, most cybersecurity experts recommend using Monero while shopping on darknet markets.
Agora Reloaded – Restore Ratings and Vendor Bond Waived for Old Agora Vendors, AUTO Import ALL Listings from Dream Market, ALWAYS UP, Check it! The drug cartel is impressed with your hacking skills, and they agree to adjust the pricing of their international trade according to your model. Today’s COVID-19 reimbursement funds will be spent without any assurance of more, although the need for financial support won’t go away. This article shows how it works and how you can get started. It’s just another incarnation of the new kind of trust-building that technology has facilitated.
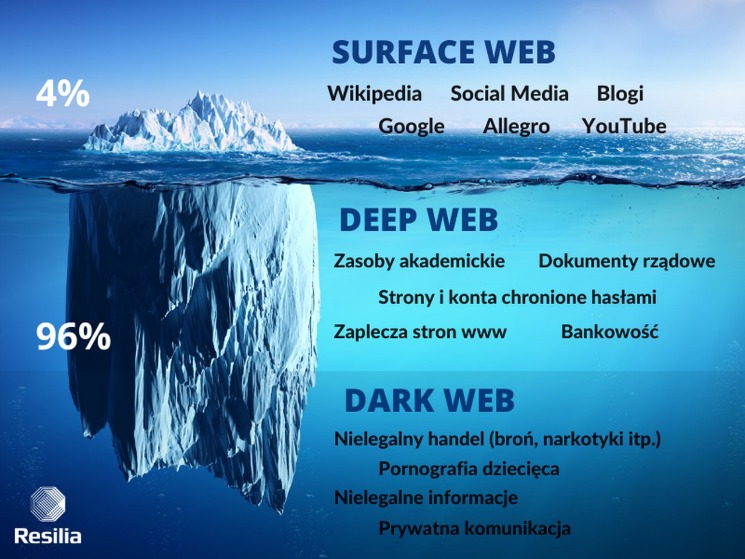
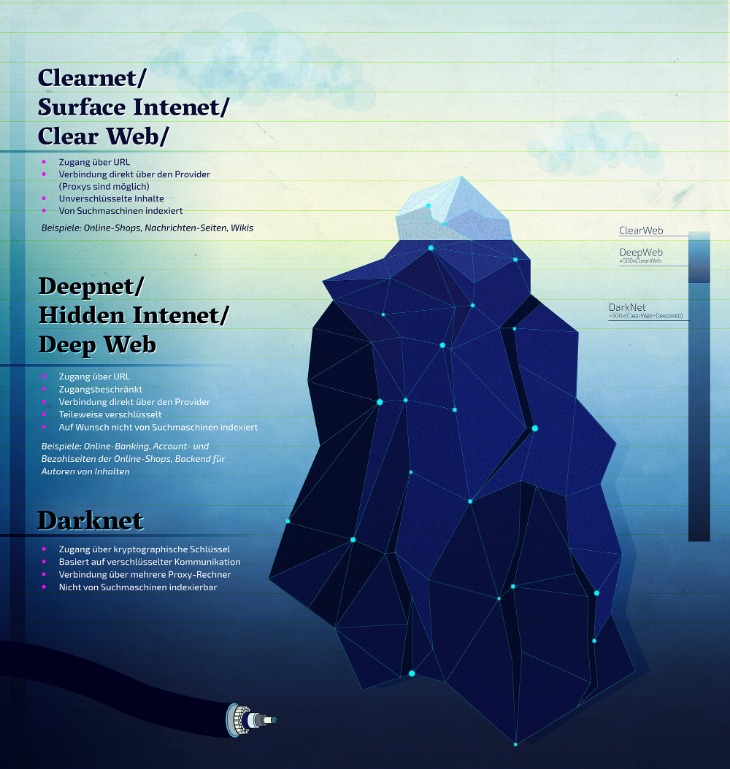
Darknet markets, in particular, have gained attention for their role in facilitating the exchange of illicit goods and services. Despite their controversial nature, these marketplaces continue to evolve, offering a glimpse into the darker side of online commerce. As cyber threat intelligence professionals monitor these markets, they gain insights into emerging threats and malicious activities that can impact organizations and individuals. There are a lot of misconceptions about the dark web online and in popular media.
Your email address is used only to let the recipient know who sent the email. Neither your address nor the recipient’s address will be used for any other purpose. The information you enter will appear in your e-mail message and is not retained by Tech Xplore in any form. In 2013, the FBI shut down the Silk Road website. Track and analyze darknet activities using our advanced cyber threat intelligence platform to stay ahead of emerging threats. Buying illegal substances, stolen merchandise, and counterfeit currency or goods online poses significant risks for both the buyer and the seller.
Key Cyber Threats Facing The Financial Sector In 2025
Reputable markets have measures to protect buyers and sellers. This ensures buyers commit funds upon order, but sellers only get paid upon delivery. Never accept a special offer to bypass an escrow system, or to enter into private negotiations. On some sites, sellers pay a deposit or bond to the market, which they forfeit if too many customers complain. An eBay-style reputation system is also necessary. Learn how your chosen market works, and how it protects its traders.
Ponzi schemes promise high returns with little to no risk. Early participants may see some profit, but that money usually comes from new victims, not actual earnings. Eventually, the system collapses, and most people lose their entire investment. So, if a “business opportunity” sounds too perfect, it probably is.
This is extremely dangerous, because overdosing is often the result of not knowing the purity, dosage, or content of the drug you take. Cannazon is a cannabis only market with a focus on the European community. Instead, the only choice is to look toward privacy coins that obfuscate sender and recipient data. Making a Purchase When making a purchase and going through the checkout you will be prompted to select a payment method.



