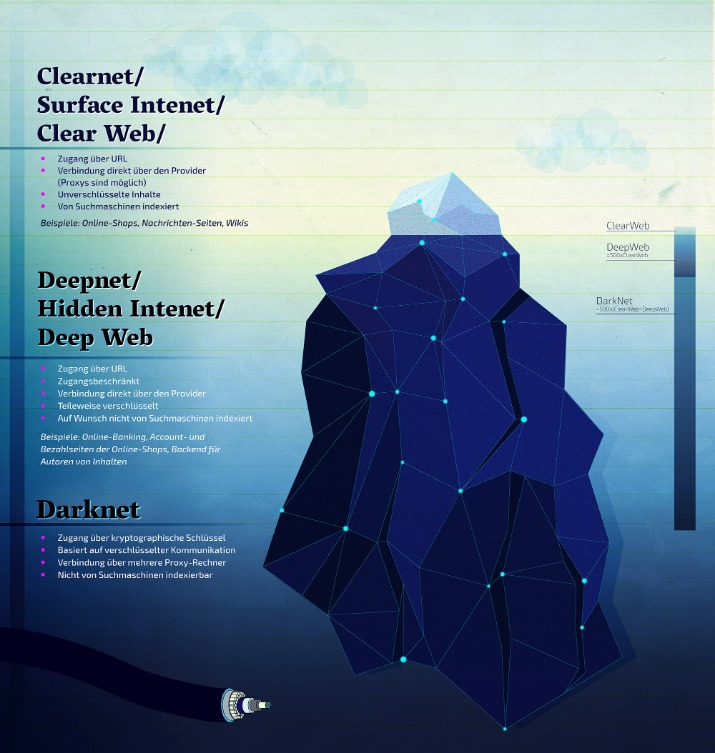
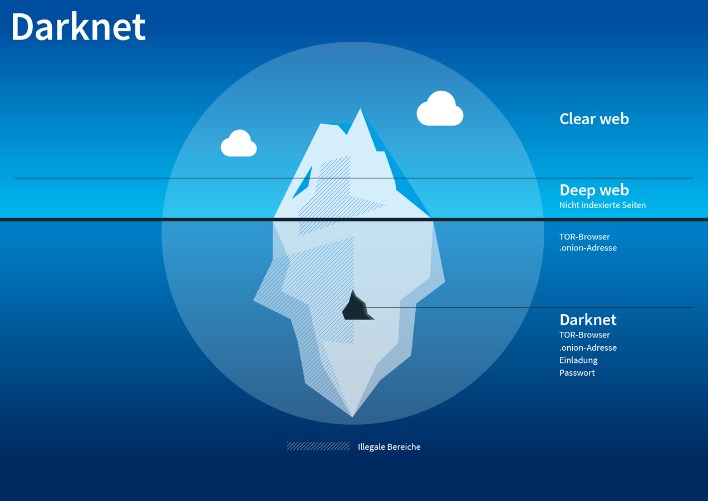
Sites on the dark web use .onion domains, which are only accessible via the Tor browser. The Tor network adds a layer of anonymity, which helps dark web sites remain hidden and makes it impossible for conventional search engines to index them. However, these search engines serve as an entry to the internet’s underbelly.
DuckDuckGo — A Dark Web Search Engine
You can also run a dark web scan to see if your information has been leaked on the dark web. This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks. Unlike other search engines, it does not collect or share web activities and personal data of users.
Darknet Market Search Engine

The platform is also used by governmental cyber departments to identify and track potential criminals or offenders. You can never be sure who’s really behind the other end of the line. Now that you’ve completed the download, it’s time to install the Tor browser on your device.
Words Of Caution When Using Dark Web Sites
While it might be tempting, remember that downloading such content has serious legal and cybersecurity risks. This can include everything from full names, email logins, and passwords to credit card details, social security numbers, and bank account information. The cybercriminals trade even sensitive documents, such as medical records, passport information, and driver’s licenses.
How Can I Verify A onion Site’s Authenticity?
- Note that engaging with the content in any way is not only distressing but could also put you at legal risk.
- Blockchain even has an HTTPS security certificate for even better protection.
- With a single click of a button and going through some web pages, one can now easily visit a dark web page.
- Despite their controversial nature, these marketplaces continue to evolve, offering a glimpse into the darker side of online commerce.
- The dark web’s anonymity is one of its primary security features, and violating it can make you a target for identity theft or phishing.
Ensure that your Tor browser and security software are always up to date. Outdated software may contain vulnerabilities that allow exploits to bypass the online anonymity provided by the Tor network. Even the best privacy tools are only effective when patched against the latest threats. The dark web is bottomless and continues to grow each day, and so does the number of tools used to get around in it. Here’s a breakdown of the most commonly used dark web search engines in 2025.
PRIVACY ALERT: Websites You Visit Can See These Details About You:
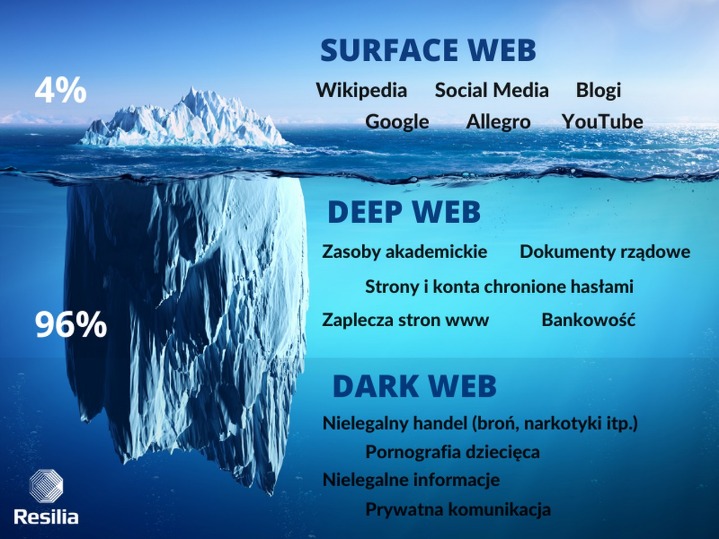
It’s simply a part of the internet that isn’t indexed by regular search engines and needs special software, like Tor, to access. However, while browsing the dark web itself is lawful, taking part in illegal activities — like buying or selling illegal goods or engaging in criminal behavior — is not. To stay on the right side of the law, be cautious about what you access and ensure you follow the rules in your region.
These groups develop their own sophisticated malware, sometimes combined with pre-existing tools, and distribute them through “affiliates”. There are also many tools that can be use to monitor the dark web and scan for personally identifiable information and even respond to attacks. Downloading files from the darknet can be risky, as they may contain malware. It’s best to steer clear of any downloads unless you are certain of the source’s credibility. It routes your connection through multiple encrypted nodes, ensuring anonymity. Flare integrates into your security program in 30 minutes and often replaces several SaaS and open source tools.
This search engine will get you to the sites you need, though you can also go directly to dark web addresses if you know what they are, as with standard URLs. Tor sites are unstable, with most of them often being under construction. This leads to data loss, content changes, and inconsistency in the quality of results. Sites are often shut down and backed up as admins try to avoid being caught.
Protect Yourself
Enable MFA wherever possible to protect your accounts from unauthorized access. ZeroBin is an attractive option for anyone looking to share sensitive information without compromising privacy. It’s particularly useful for journalists, whistleblowers, and those who urgently need to send or receive confidential data.
The platform stood out during my testing for its commitment to anonymity — all messages are fully encrypted and stored on a decentralized network. It’s particularly useful for sensitive communications that need to remain private. Proton Mail’s dark web version provides end-to-end encrypted email with enhanced privacy protection. The service doesn’t require personal information to create an account and works seamlessly through Tor.

Plus, there’s a thorough vetting process for new buyers and sellers to keep the community more secure. In a way, it feels more like a private club than an open market, and that’s exactly how the operators want it. It indexes a wide array of content, including both legal and illegal sites. While it primarily indexes the surface web, it can also be accessed via the Tor browser and used as a general search engine. Unlike the regular internet, the Tor network can’t be accessed via standard browsers. We set out to build TorDex to be fast and user-friendly, ensuring that it delivers meaningful results without limiting what can be indexed.
Is It Safe To Use A Dark Web Search Engine?
The Hidden Wiki functions as the dark web’s counterpart to Wikipedia. Although it’s not a search engine, it offers a categorized directory with indexed links to .onion web pages. While the Hidden Wiki isn’t entirely unrestricted, and uses filters to block many dangerous sites, it still lists some dubious sites that other search engines block. Torch is one of the oldest and most well-known dark web search engines, providing access to a vast index of .onion websites. Unlike many dark web search engines, Ahmia is accessible on both the surface web and Tor, allowing broader access to its indexed content. It all starts with Tor, which keeps your identity under layers of encryption.



