
Arresting vendors often has a greater disruptive impact than taking down DNMs. When a marketplace is shut down, vendors can typically migrate to other platforms. But when a vendor is arrested, their activity is disrupted across every DNM they operate on. As a result, law enforcement has adopted an intelligence-led enforcement strategy incorporating DNM takedowns into longer-term investigations rather than treating them as end goals. However, when a DNM collapses — especially a large and reputable market — its users typically migrate to the nearest available platform.
The White House market offers impressive features like a mandatory PGP requirement that enables 2FA for the user’s profile and adds a protective layer. During our tests for the research, we were able to register with a bogus email and a random username. All that one can expect from a deep web marketplace when it comes to anonymity and security. We The North Market is built for secure, trusted transactions with some of the lowest vendor fees in the industry.
The History Of Darknet Marketplaces
- ProPublica aims to bring controversial, repressed stories into the open for all to see.
- Don’t ever reveal your true identity on the dark web marketplaces because there’s a high chance of hackers and scammers misusing it.
- Once a buyer makes a payment, it’s usually held in escrow until they receive what they bought.
- To prevent the users from DDoS attacks, it provides personal marketplace domains to high-volume buyers and sellers.
- There are currently several online darknet markets, but they tend to be incredibly volatile due to government intervention.
You can also run a dark web scan to see if your information has been leaked on the dark web. This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. Many people see hacked information and stolen card data being sold on the dark web.
Protecting Against Malware And Exploits

The Torrez market is one of the biggest dark net marketplaces, also called a community-driven marketplace. It contains a good selection of product listings that range over 35,000 items. The website has an interface and design similar to other dark web shops. It uses PGP encryption, two-factor authentication, and OPTP authentication to ensure users’ security.
Secure Your Cryptocurrency Transactions
Unlike Bitcoin, which records every payment on a public ledger, Monero conceals all transaction details by default, which makes them nearly impossible to trace. The durability of these markets tells us that if policing responses keep following the same playbook, they will keep getting the same results. And by focusing so heavily on these hidden platforms, authorities are neglecting the growing digital harms in the spaces we all use. Last week, one of the dark web’s most prominent drug marketplaces—Archetyp—was shut down in an international, multi-agency law enforcement operation following years of investigations. It was touted as a major policing win and was accompanied by a slick cyberpunk-themed video. Typically, you can find dark web URLs through forums, databases, or by talking to others who frequent those sites.
What Is The Dark Web And How To Access It?
Some dark web listings claim to offer services like hacking-for-hire or even hitmen. In this article, we’ll explore what dark web markets are, how they work, and why they’re so risky. We’ll also discuss examples of major marketplaces, myths about the dark web, and tips on staying safe in case your personal data ever ends up there. George is a seasoned Cybersecurity writer who has been writing guides and news about digital security for over five years. He has worked for several international tech platforms, and his writing and editing expertise has also enhanced over time. He loves covering topics about VPNs, online privacy, and anonymity and shares his knowledge of online security with internet users through his words.
Plus, there’s a thorough vetting process for new buyers and sellers to keep the community more secure. In a way, it feels more like a private club than an open market, and that’s exactly how the operators want it. Now that you understand what the dark web is all about, you might wonder why other people do things on it. Darknet marketplaces like to exist on the dark web because it offers a service that the regular internet, or more accurately, the “surface web,” does not. Users and cybersecurity professionals alike must stay informed and prepared to navigate this rapidly changing digital frontier. Overall, Abacus Market distinguishes itself through rigorous security measures, effective moderation policies, and a strong emphasis on protecting user privacy.
Common Scams And Fraudulent Activities On Darknet Markets
In 2025, the darknet continues to serve as a hub for secure and efficient drug trade, with platforms evolving to meet user demands for privacy and reliability. The integration of advanced encryption technologies and decentralized systems ensures that transactions remain confidential, while user feedback mechanisms enhance trust among participants. The darknet has become a cornerstone for secure and efficient drug trade, offering users unparalleled privacy and reliability. By 2025, several platforms have emerged as leaders in this space, leveraging advanced encryption, decentralized systems, and user-friendly interfaces to ensure seamless transactions. These advancements will further solidify their position as a secure and reliable option for users worldwide. The rise of verified market lists has further simplified access to these platforms, ensuring users can connect to legitimate and secure marketplaces without the risk of phishing or scams.
Dark Web Reveals Tech Companies Leak Most User Data
It also includes a dark web monitoring feature that crawls the dark web and alerts you if your details show up anywhere. For these reasons, it’s a good idea to safeguard your online activities with NordVPN while using the dark web. Ahmia is a safe alternative search engine for users who prefer the dark web. It also provides insights, helpful statistics, and updates regarding the Tor network. When you access this site, do so with extra protection, even if you are technically anonymous when you use the Tor browser. We highly recommend using a strong VPN like NordVPN to stay safe and private.

- You can choose the best darknet (.onion) website that suits you and start surfing.
- Such companies’ tools enable investigators to trace administrator wallets and follow illicit flows even after a marketplace goes offline.
- These shifts tie into how markets like these are evolving—check them out below.
- It includes all the essential productivity software, including MS Word and an email client.
- Policing involves targeting specific activities of the private web deemed illegal or subject to internet censorship.
But if you still decide to access these websites, for education or research purposes, make sure you stay cautious. Although dark-web marketplaces utilize technologies like Tor and I2P to enhance anonymity, these methods are not foolproof. Law enforcement agencies continuously improve their ability to trace transactions and monitor marketplace activity. Simple mistakes—such as inadequate operational security practices, sharing identifiable details, or using compromised devices—can quickly compromise anonymity and expose users’ real-world identities. Understanding both the lawful and unlawful scenarios helps provide a balanced view of their practical applications in 2025.
What Kind Of Content Is On The Dark Web?
Remember that phones can get viruses just as easily as computers, and the chances of getting a virus likely increase when you’re browsing dark web mobile sites, no matter your platform. For cryptocurrency enthusiasts, Wasabi Wallet is considered an indispensable trading tool and one of the safest ways to buy, sell, and manage cryptocurrency on the dark web. Wasabi Wallet isn’t free to use, but, for a small fee, you get reliable and anonymous cryptocurrency transactions. Even passive activity on these sites can contribute to criminal networks. For instance, buying fake documents may indirectly support larger operations involving trafficking, extortion, or organized crime. If the websites you visit use tracking scripts, third parties can monitor you.

Once it lands on a darknet marketplace, it becomes part of the illegal weapons trade. BidenCash is another latest marketplace that started in 2022, and is now home to sensitive financial data transactions. This is where cybercriminals go to buy and sell things like stolen credit card numbers, personally identifiable information (PII), and even SSH login details. One thing that distinguishes BidenCash on the dark web, however, is how it markets itself. One of the things STYX is infamous for is having a rigorous verification process for users that makes it seem more exclusive.

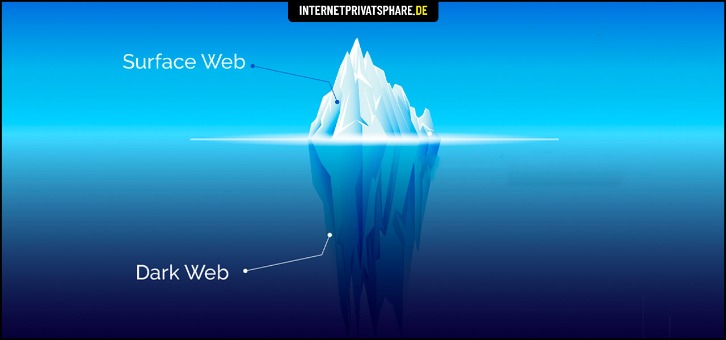
This service not only masks your IP address but also encrypts your data, adding an extra layer of security. By using Forest VPN, you ensure that your internet service provider (ISP) and other potential eavesdroppers cannot trace your online activity back to you. Other dark web search engines worth investigating are Ahmia, Torch, NotEvil, and the Onion URL Directory—just type out some keywords for what you’re looking for. Some of these sites can be found through regular web browsers, but you’ll then need to switch over to Tor once you’ve got the onion links you want to follow. The dark web, which is what I’m discussing here, is a small subset of the deep web, and refers to websites that are specifically trying to stay out of sight.



