Figure 8 is an example of a sample of an Australian passport template which has the same passport ID details but has different photos of individuals. The seller of the below template also shares that any details in the passport including the photograph can be changed and it would still look legitimate. The seller provides full editable versions of the template in .psd format which is an Adobe Photoshop document format. The seller also provides download links to cracked versions of Adobe Photoshop so the buyers can use the .psd files without needing to buy a licensed copy of the software.
The Digital Black Market For Identity Data
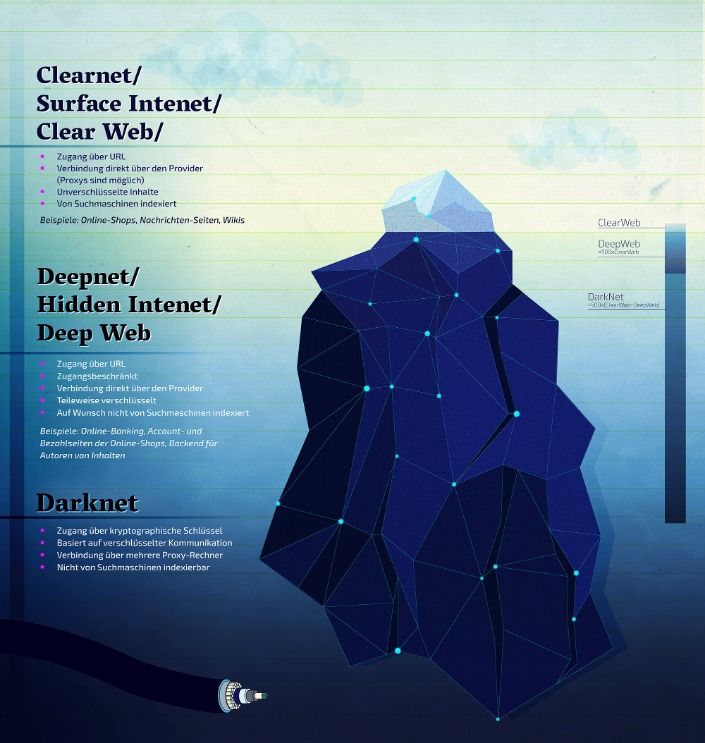
However, not all usage of the dark web is for illegal intent. Social networks, such as Facebook, have created dark web versions of their sites to address privacy problems related to their surface web versions. ExpressVPN had created a .onion version of its website to allow greater privacy and anonymity for Tor browser users. However, the link to the site appears to no longer work. You don’t need special tools or a special browser like you need to access the dark web (more about that later).

Explicit And Illegal Content
If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address. Commenting on the findings, Andrew Newell, Chief Scientific Officer at iProov warned against selling personally identifiable information to anyone. Hackers have found an easy and simple way to grab people’s sensitive information, and then use it to bypass Know Your Customer (KYC) processes – buying the information directly from the victims. At Digital One Agency, we’re here to help you build legitimate, secure, and profitable tech ventures — the kind that scale, attract real customers, and don’t end with handcuffs or disappearing acts. While this dive into darknet tech is fascinating, don’t take this as a blueprint.

Counterfeit Factory
So, sites that contain a domain extension like .com, .org, .net, .biz, .info, etc. can be found on the surface web. In addition, the content on the pages don’t need any special or custom configuration to access. Pixel Privacy believes in digital privacy and does not believe in using it for heinous and/or illegal activities, and so the focus of this article will be on legal activities.
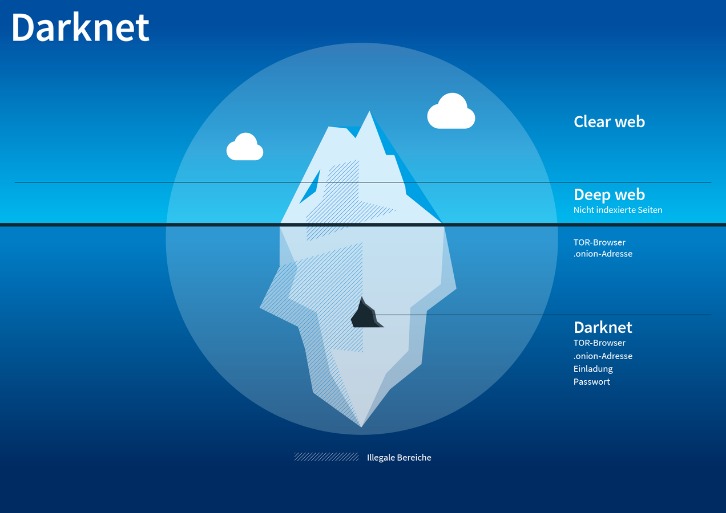
The many ways in which stolen data can be misused are complex and do not end here. Darknet markets are websites which are hosted on the deep-web and can be accessed typically using the Tor network. Stolen data has greatly increased in trading value on the Darknet. The expansion of data trading can be attributed to several factors. The increase in data breaches and data leaks has led to more personal data being available for trading on the darknet.

New Shamos Malware On Mac: Beware Of ClickFix Attacks
Darknet markets are hidden websites which cannot be accessible using regular browsers or search engines as they do not have an actual DNS name. Most darknet markets have a .onion TLD suffix which states that it is a hidden service and can only be reachable by the TOR network. A .onion site consists of 16 alphanumeric characters followed by a .onion TLD. The 16 characters may include letter from ‘a to z’ and numeric numbers from ‘1 to 7’. Dark web markets have exploded in scale and reach in 2025, becoming the most dangerous hubs for trading drugs, stolen data, and hacking tools. These anonymous marketplaces—operating mainly on the Tor network—are now a primary threat vector for businesses and cybersecurity professionals.
Plus, cryptocurrency transactions are fast, reliable, and protected by blockchain technology for added security. Users who wish to gain access to such information are protected by the same anonymity the publishers of the content enjoy. Well-known news websites, such as ProPublica, have launched deep websites.
Introduction: How Much Of The Internet Can You See?
WeTheNorth has a strong community vibe, with an active forum where users interact and share updates. Purchasers ranged from underage individuals seeking entry to clubs and bars to criminals engaging in identity theft and money laundering schemes. Listings for fake documents typically detail the quality of the forgery, the region or jurisdiction covered, price ranges, and turnaround times. Vendors often showcase sample images and customer reviews, reinforcing credibility and trust.
- Despite its name, the marketplace operates primarily in English and serves a global audience.
- All products comes with 1 year warranty by Apple and ready for registration.
- Some dark web listings claim to offer services like hacking-for-hire or even hitmen.
- The market claims to provide secure and anonymous commerce services.
- They don’t offer hacking services at this dark web site.
Fraudulent Markets
The Identity Theft Research Center reported that 1,291 breaches had occurred till October 2021, compared to a total of 1,108 in 2020. The 17% rise indicates that higher numbers are on the way, making it more necessary than ever to safeguard identity data. The collection, purchase, or trade of customer data is big business. Unless organizations and individual entities take necessary precautions, that information may be at risk. Once this data is compromised, there’s a high possibility of losing rights to it forever.
A dark web search engine like DuckDuckGo offers impressive anonymity features and makes it easy to access the shops. These search engines neither track your search queries nor record any information, improving digital privacy and keeping your data private. DarkFox Market is the largest dark web shop selling various products and attracting more vendors and users. It is a wallet-based shop, meaning you must first deposit bitcoins into your wallet before purchasing any goods and services. The marketplace is much more organized, which makes it easy to use and navigate. Using a reliable VPN provider helps keep you safe when you access marketplaces on the dark web.
To access this marketplace, you must register, but before that, you must verify yourself as a human by passing a CAPTCHA test. This guide outlines different ways of safely accessing dark web stores and the list of reliable dark web marketplaces you can consider visiting in 2025 for research and monitoring purposes. The digest is the base32 encoded value of the first eighty bits of a SHA1 hash of the identity key for a hidden service. Once Tor sees an address in this format it tries to connect to the specified hidden service. Many darknet market users also use a VPN network to add an additional layer of privacy to hide their source.
All possible user’s queries are answered here like other dark web links. This dark web site offers genuine documents, registered in their respect database system. Documents include passport, driver’s license, ID card, SSN, Diplomat, degree, resident permit, and printing documents.
After the cyberattack on the Bernese IT company Xplain in May 2024, stolen data was published on the darknet. An analysis by the Federal Office for Cybersecurity (BACS) revealed that around 65,000 of the 1.3 million data records published were relevant to the Federal Administration. Around 9,000 of these documents could be attributed to the Federal Administration, with around 14 percent containing sensitive content such as personal data, technical information, classified data and passwords.
- KEY TAKEAWAYS The Deep and the Dark web are the hidden part of the internet.
- Not all personal information is valued the same on the dark web.
- The global networking of such forums makes it difficult to protect against these threats, as stolen data is traded anonymously and without geographical restrictions, regardless of its origin.
- If you purchase more than 2 cards, you will get discount.
- This includes evidence of any websites you visit, files you open, passwords you use, and even any other devices or networks you connect to.
They use these, for example, to sell illegal goods, whereby the traces initially lead to the actual owner of the hacked account, while the perpetrators remain hidden. Stolen data can also be used to blackmail or expose those affected. Perpetrators threaten to publish sensitive information in order to extort ransom money.



