
It added that many fraud shops are increasingly offering third-party crypto-payment processors like UAPS via API calls, as a way to reduce their own costs, improve operational efficiency and increase security. Layer a VPN (e.g., NordVPN) to mask your IP before entering darknet markets. A timeline of darknet marketplace evolution, from Silk Road to 2025’s top players. Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP. It is considered a go-to site for malware purchasing, providing keyloggers, trojans, and other Malware as a Service products. Established in 2022, Torzon market is one of the biggest and most diverse marketplaces on the dark web.
Abacus Upgrades

Just because the seller has good reviews does not mean you can trust them. There’s nothing stopping sellers from packing up and leaving the market at any time. They could get a batch of bad products, get arrested before they can ship your order, or any other number of things. There’s no guarantee that placing an order with any DNM vendor will be safe or shipped.
How To Access Darknet Markets Safely
With tricks like ring signatures and stealth addresses, it keeps your transactions off the radar—unlike Bitcoin, which can leave a trail if you’re not careful. Most markets, like Abacus or Archetyp, love it for that privacy kick. Darknet markets trace their origins to the early 2000s, with the advent of Tor in 2002 by the U.S. The first notable marketplace, Silk Road, launched in 2011 by Ross Ulbricht (aka Dread Pirate Roberts), revolutionized online black markets by integrating Tor, Bitcoin, and an escrow system. The primary technology used to access the Dark Web is the Tor network, which allows users to maintain anonymity and privacy while accessing websites and services. To remain anonymous about your purchases on the dark web, always use cryptocurrency as your mode of payment.
What Is WPA2 (Wireless Protected Access ?

We review and list tools and products without bias, regardless of potential commissions. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page. Get in touch today to see how we can help you detect, deter, and disrupt illicit operations while ensuring compliance with global AML regulations. As always, we must caution that these figures are lower-bound estimates, especially so for off-chain crimes, as many scams and fraud go unreported. The Chainalysis Crypto Investigations graph below demonstrates this type of behavior in a known scam group targeting the elderly.
AlphaBay Market
Its emphasis on user anonymity and document forgery makes it a core tool for identity fraud. Launched after the takedown of AlphaBay in 2021, Abacus Market has rapidly risen to prominence. It features over 40,000 listings including narcotics, counterfeit items, hacking tools, and stolen data. The marketplace is well-known for its bug bounty programs and robust security mechanisms, including mandatory 2FA.
I grabbed mine from the official site a while back after dodging a sketchy mirror that tried to sneak in some junk software. Even though the links are PGP verified, that doesn’t mean the sites are 100% safe. I did not send any money or made any purchases, so I can’t vouch for any of the sites listed. While there are legitimate uses for the dark web, such as protecting privacy and freedom of speech in repressive regimes. It remains predominantly known for its association with cybercrime, drug trafficking, hacking, and other criminal endeavors.
It has gained a reputation for being a reliable source of high-quality data for cybercriminals. Due to its extensive inventory and reputation for reliability, Brian’s Club has maintained a significant presence on the dark web. Quality and validity of the data it provides justify its higher cost over other marketplaces. The platform’s popularity continues to grow, attracting both new and returning customers. To expand their reach, some marketplaces established parallel channels on Telegram.
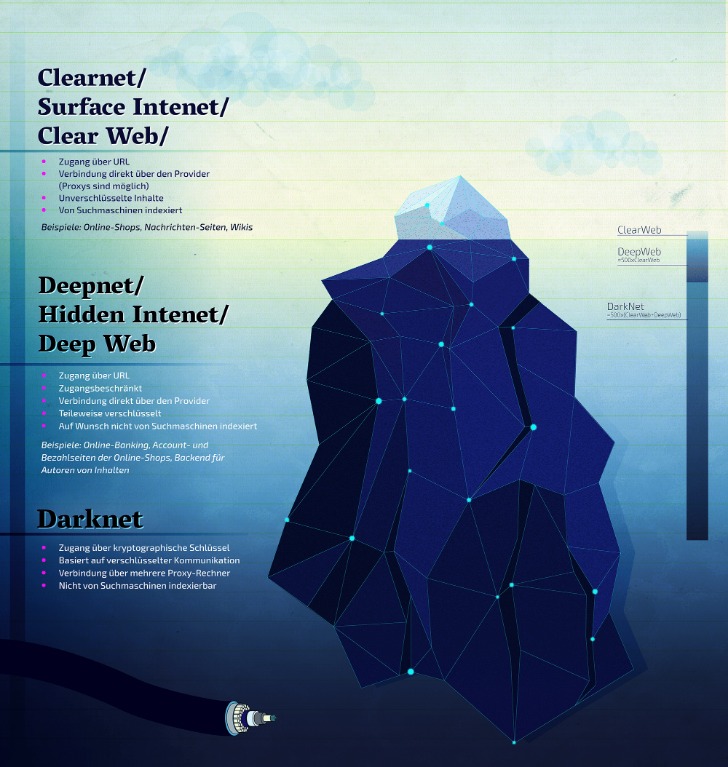
- You can only access it using special software, settings, or authorization.
- The darknet markets keep on popping even when the authorities keep getting hard on them.
- According to a threat actor who posted the offer for 210,000 JPY, exploiting this vulnerability could grant NT Authority/System privileges, meaning a high level of permissions.
- Therefore, you need to start by changing your passwords, and you need to notify your credit card or bank provider.
The number of sellers in each category and multisellers as a function of time is shown in Fig. Until the end of 2013, when Silk Road is the dominant market (see Fig. 3), market-only sellers is the dominant category, and there are no multisellers. From the last quarter of 2013, U2U-only sellers become the largest category of sellers and remains as the largest throughout the rest of the observation period. Our classification shows that the number of sellers is significantly smaller than the number of buyers, as shown in Figs. The number of actors in the ecosystem is affected by several factors, especially market closures. Notably, the number of buyers and sellers significantly drops after the operation Bayonet in the last quarter of 2017, which shut down AlphaBay and Hansa markets, causing a major shock in the ecosystem34.
How Can I Enhance My Privacy While Accessing The Dark Web?
In the vertical axis, markets are in the chronological order of their launch date, although for some markets the activity effectively starts after the launch date (e.g., AlphaBay). You can use a dark web scan tool to tell if your data has landed on the dark web. The tool scans the dark web marketplaces and forums for signs of compromised personal credentials. The darknet markets keep on popping even when the authorities keep getting hard on them.
Is There A Future For Dark Web Marketplaces?
- It is home to all sorts of disturbing content, given that the markets share content related to non-consensual recordings and child exploitation.
- Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks.
- This site supports PGP encryption and two-factor authentication features.
- Rather, the launderer might split funds off into many disparate wallets and then reconsolidate the funds later, after multiple transactions.
- To remain anonymous about your purchases on the dark web, always use cryptocurrency as your mode of payment.
It is assessed that only a minority have used it personally (see “Darknet Use in Southeast Asia” in Appendices). Even on the news, the Darkweb is generally not discussed in any great detail, with most stories relating to the arrest of cybercriminals who have used the Darkweb in some way. Markets overwhelmingly use XMR to avoid traceable Bitcoin transactions. Monero’s ring signatures, stealth addresses, and RingCT obfuscate transaction details—enhancing privacy and hindering traceability The Rise of Monero.
The darknet is used for anonymous communication, accessing censored information, and protecting privacy. Journalists and activists use it to communicate securely in oppressive regimes. You can access it for legitimate purposes like whistleblowing and freedom of expression. However, it’s also used for illegal activities like drug trafficking, weapon sales, and stolen data trading. Law enforcement agencies monitor it for criminal activities, but legitimate users rely on it for privacy protection. In order to investigate the role of direct transactions between market participants, we now analyse the evolution of the S2S network, i.e., the network of the U2U transactions involving only sellers.
Sellers often need to pay a deposit to prove they’re serious, and they build their reputation through positive reviews. While accessing Darknet Markets themselves is typically not against the law in most places, engaging with illicit goods within them is generally considered a crime. On the other hand, some people might visit Darknet Markets for lawful purposes such as research, journalistic work, or simply to explore online communities. It’s essential to know the local laws regarding online activities, and be cautious when using these platforms to avoid any potential issues. TRM Labs reports that both its clearnet mirror and hidden-service infrastructure became inaccessible, and the site’s operator, known only as “Vito,” vanished along with users’ escrowed funds. Darkweb-related arrests in Southeast Asia have helped focus attention on how transnational organised crime groups and syndicates operate in the region.
These critical changes may not be perceived from macroscopic measures of the ecosystem as a whole. For instance, the typical net income of sellers is seemingly unaffected, as shown in Fig. 2a, where the overall ecosystem volume quickly recovers after market closures. This is an outcome of the ecosystem’s resilience, largely supported by the migration of users15.
Trading Tips
Further market diversification occurred in 2015, as did further developments around escrow and decentralization. KEY TAKEAWAYS Whether you are using Android or iPhone, you can easily access the dark web on your ph… KEY TAKEAWAYS The Deep and the Dark web are the hidden part of the internet. When you use it, all the web traffic automatically routes through Tor. If the operating system detects any non-anonymous connection, it blocks it, thus ensuring maximum online protection. Since the dark web can be accessed through the Tor browser, use a VPN with the Tor browser to ensure increased protection.
Monero (XMR): Darknet’s Currency
These funds flows suggest that crypto is now being used as a common tool for fraudsters to launder their stolen funds. Further expanding the aperture, we identified over 1,500 consolidation wallets that have received a total of $2.6B worth of bitcoin in 2024; each of those have received funds from at least ten different wallets. Again, we cannot say for certain that this represents money laundering — in fact, much of it likely represents legitimate inflows.



