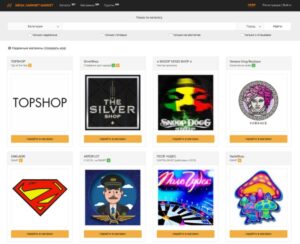
It is a wallet-based shop, meaning you must first deposit bitcoins into your wallet before purchasing any...
Having payment cards cloned can be utterly catastrophic for victims, yet for the cybercriminals stealing the information,...
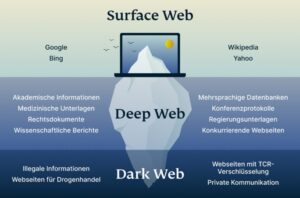
Most people start by using the Tor Browser, which hides your IP address. One of the most...
The encryption technology routes users’ data through a large number of intermediate servers, which protects the users’...
Back then, the dark web was a niche curiosity for cyberpunks and tech rebels. Fast forward to...
For example, users migrate to alternative DWMs when a DWM that they trade on closes12,13. Such migration...
Silk Road was one of the first darknet markets, but in 2013, the FBI shut it down....
In 2025, it powers 2.5M+ daily users, with Germany leading in usage (followed by the U.S.). In...
Thanks to the evidence Stefan and his team gathered on the Robertsson brothers, Swedish courts were able...
Thieves often buy cards to use on specific sites that don’t have security features like Verified by...