The more proactive you are, the better you can protect yourself against identity theft and other cyber...
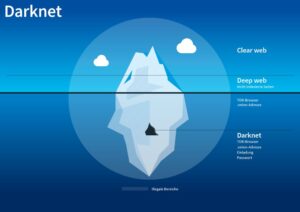
darknet
Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating...
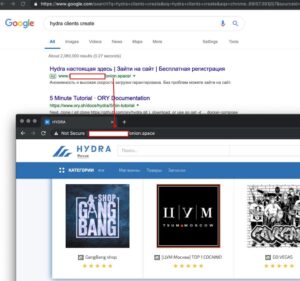
Users must look for platforms employing robust encryption protocols, secure escrow services, and advanced anti-phishing measures. Additional...
Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed. Besides, victims...
Since its inception, Abacus Market has gradually increased its market share in the Western DNM ecosystem. In...
As these platforms continue to innovate, they are likely to attract even more users, further solidifying their...
The platform also cares about its users and uses PGP encryption and two-factor authentication to secure their...
CACI’s DarkBlue Intelligence Suite is designed to address these exact challenges, offering comprehensive monitoring and analysis of...
Based on our observations from analysis on dark web data using Lunar, we’ve identified the top 7...
The most interesting thing about NordVPN is its built-in Onion over VPN feature. It encrypts your traffic...