
Helped by the launch of Bitcoin in 2009, the dark web quickly became a platform for criminals to source and deliver illegal items. Encountering or inadvertently engaging with this material can have serious legal and ethical repercussions, putting you at risk of legal action or psychological harm. Accessing the deep web doesn’t require a special browser or unique protocols. The dark web, however, can only be accessed through the Tor browser. The encrypted nature of the browser means everyone trying to access the dark web remains anonymous by default.
LostMyPassword – Dual Use Password Recovery And Credential Dumping Tool
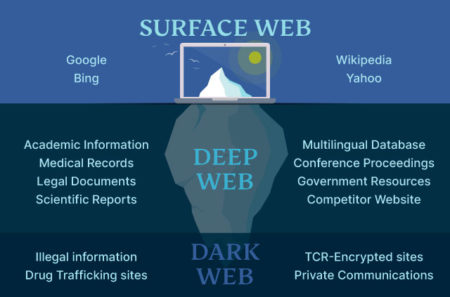
Search engines like Google can’t access the Deep Web and Dark Web simply because their content is not indexed. This lack of indexing of its content makes these layers of the internet less easily accessible and harder to navigate than the Surface Web. Hence, the deep web encompasses the dark web which constitutes a relatively smaller section entirely hidden and requires software specialized as Tor to access.
Deep Web pages include personal pages like webmail inboxes and account pages on various sites. They also include internal company data and sites that are accessible via the Internet but protected by authentication. Although the Dark Web is often used for illegal activities, it’s not illegal to access it in many countries. Some people use the Dark Web for legitimate reasons, but prefer to remain anonymous. What most people think of as the “Internet” or the world wide web is actually what is known as the Surface Web, or Clear Web. This is the part of the Internet that is visible to search engines like Google and accessible via normal web browsers.
Understanding The Layers Of The Web
The good news is that there is a much faster version of privacy technology that is similar to Tor, albeit much faster. A VPN is a technology that (like Tor) provides you with a string layer of encryption to stop local networks, ISPs, and government agencies from being able to monitor your online activities. To access the purposely hidden part of the internet, you have to use special tools such as the Tor browser.
- If you come across software that seems neat and valuable, do not install it.
- The information that one shares through Tor are always encapsulated through secure tunnels like onion layers to reach its destination.
- The creation of the open-sourced Bitcoin in 2009 by Satoshi Nakamoto played a crucial role in this development.
- MFA protects you in the event that someone gains access to your login credentials since it requires a one or more methods of authentication before they’re able to successfully log in.
- Standard search engines index these websites and are accessible without special configuration.
Difference Between Deep Web And Dark Web
However, even in places where it is technically illegal, there isn’t much the authorities can do to stop people from accessing it. Remember, the deep and dark web is encrypted and only accessible in specific ways. Due to this design, it is difficult for governments to stop it even if they legally prohibit it. What is illegal in every jurisdiction is using the dark web to acquire illicit products or services. Darknet provides a user with anonymity but a service was introduced that allowed someone to host a website on the darknet and remain anonymous.
What Types Of Content Exist On The Deep Web?
The Gray Web is referred to the part of the Surface Web where fraudsters discuss or research their activities. However, the Surface Web represents only the tip of the iceberg when it comes to the internet – the majority of it is actually hidden. This part of the web contains everything from password-protected sites and data not accessible via public web pages to private intranets, academic content, and more. It makes up about 99% of the entire web and is largely inaccessible to normal users. Cyber criminals phish users and exploit vulnerabilities in websites, databases, networks, and web apps to gain access to confidential data, such as user credentials. This information is then often traded or sold on underground online platforms, commonly known as the dark web.
Staying Safe On The Deep And Dark Web
The Dark Web, which is only accessible via special web browsers, uses the same network infrastructure as the Surface and Deep Web but is completely distinct from it. The deep web refers to hidden web pages that are not indexed by search engines. This lack of indexing is intentional on the part of many service providers, as it helps to protect private information. It requires specific software and knowledge to access, creating a barrier that keeps casual internet users away. Finally, law enforcement agencies can access the dark web to detect illegal activity, such as weapon deals, drug distribution, and financial crimes.
This includes password-protected websites, private databases, and other online content that is not meant for public dissemination. Users often turn to the dark web for private communication, whistleblowing, or accessing restricted information in censored regions. However, it’s also notorious for hosting illegal activities, including illicit marketplaces and hacker forums. Like the deep web, the dark web is used for positive as well as nefarious purposes. On the positive side, dissidents, journalists, whistleblowers and advocates for freedom of speech are able to express themselves on the dark web with less risk of exposing their real-world identity. Founded in 2011 and shut down by the FBI in 2013, the Silk Road was a black market for all kinds of illegal activity.

Deep Web Vs Dark Web Vs Shadow Web: What Are The Differences?
- Many popular media outlets, such as BBC, maintain an official Tor mirror site.
- In this case, two familiar people communicate with each other directly over the internet.
- There isn’t any one way to access the deep web — it just depends on what you’re looking for.
- You can use the VPN rated #1 with no restrictions for a month—great if you need time to test if it’s the right VPN for you.
- Dark web hosts project which ends with .onion (aka onion sites) and not .com, .net, .org, etc. that we generally operate with.
While the Deep Web supports daily privacy, the Dark Web offers enhanced anonymity with some added risks. Knowing how these areas work helps us make informed decisions about online safety and privacy. In the digital world, “Deep Web” and “Dark Web” often get mixed up, leading to misunderstandings. Although they share similarities, these parts of the internet serve very different purposes. Knowing the difference between the Deep Web and the Dark Web is vital for online security and privacy. All sites on the dark web end with “.onion,” as opposed to “.com” or “.org” commonly seen on the surface web.

Differences Between Dark And Deep Web Monitoring

Still, you should note that accessing the dark web without plenty of cybersecurity precautions can be dangerous for a layman. It can expose you to various dangers, which I’ll elaborate on below. If you absolutely must satisfy your curiosity on this, I will follow up with a guide on how to access the deep/dark web soon.
Protect Your Personal Information While Browsing
In a nutshell, the deep web includes anything behind login walls, while the dark web is a small, deliberately hidden portion of it. Examples of the deep web include your personal banking login portal and academic databses. Due to its association with illegal activities, the dark web has gained a notorious reputation, while the deep web is simply an invisible part of the internet where mundane activities occur. One of the most often transactioned goods on the dark web marketplaces is your data. There are tons and tons of gigabytes of leaked credentials and personal information for sale for hackers. That’s where hackers get their data for credential stuffing attacks, identity theft, and other shady business.
Is It Illegal To Access The Deep Web Or The Dark Web?
Additionally, many Dark Web sites are discoverable only via special search engines, following links from one site to another, or word of mouth. The Deep Web is a section of the Internet that is inaccessible via search engines but can be accessed via normal browsers. It is composed of “non-indexed” content that is unreachable by the web crawlers used by Google, Bing, and other search engines to find and link pages.


