
A VPN and Tor should be used together and it is advisable to connect via a VPN to Tor, rather than vice versa, for the best protection possible. If you need to access dark web resources, these are the steps you need to take. Here’s everything you need to know about this other internet, as well as how to access it. The area of the internet we access daily is known as the clear or surface web. The internet opened the door to a realm of possibilities that permanently changed the business landscape and our personal lives.
Tips For Safe Access To The Dark Web
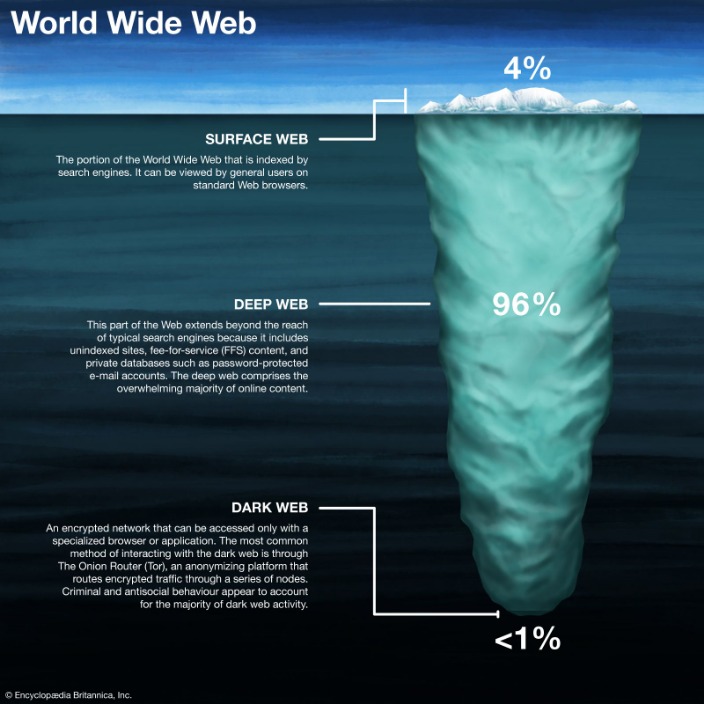
For instance, academic resources on the deep web may be found using platforms like PubMed, LexisNexis, Web of Science, or Project MUSE. The Deep Web constitutes a multifaceted realm on the Internet that evades detection and accessibility through conventional channels such as popular search engines or major web browsers. Its content remains beyond reach due to either partial indexing by search engines or the imposition of password protection measures. While the deep and dark web offer undeniable benefits, users must navigate them responsibly.
Are Sites On The Dark Web Illegal To Use And Visit?
Often, these parts of the Web are accessible only if you use special browser software that helps to peel away the onion-like layers of the dark Web. Private databases can be as simple as a few photos shared between friends on Dropbox. They also include financial transactions made on major sites like PayPal. The key feature of private databases is that people wish to share it with just certain people or preserve this information without having it publicly accessible to everyone.
Onion Links: How To Access Them

You risk being targeted for attacks if you explore the dark web without protection. The threat can extend to your entire network of devices connected to the internet. Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved.
Is The Deep Web Illegal?
Even if you never make a purchase, you could be watched and incriminate yourself for other activities later in life. The deep web rests below the surface and accounts for approximately 90% of all websites. This would be the part of an iceberg beneath the water, much larger than the surface web.
Alternative Anonymous Networks
Misuse, such as accessing illicit content or engaging in unlawful activities, undermines the value of these platforms. Conversely, by leveraging these resources ethically, individuals and organizations can benefit from enhanced privacy, improved access to information, and a safer digital presence. The Tor network, an acronym for “The Onion Router,” plays a pivotal role in accessing the dark web. Naval Research Laboratory, this technology was initially designed to protect government communications. Over time, it has become an essential tool for individuals seeking to browse the internet anonymously or evade censorship in restrictive environments.
Best Dark Web Sites: Unseen Onion And Tor Links
- In fact, when you log in to your email, social media, Internet banking, or any personal account, you’re using the deep internet.
- It would be a site that’s possibly reasonably designed, but they didn’t bother to register it with any of the search engines.
- It’s an encryption which lets you encrypt your messages, E-mail and other communication so that it can’t be intercepted by govt.
- Visit us to discover more and become a part of our growing community dedicated to exploring the depths of the internet.
- For example, in 2016, investigative news outlet ProPublica launched a hidden version of its website on the dark web to provide a secure and anonymous way for readers to access its content.
- The terms deep web and dark web are sometimes used interchangeably, but they are not the same.
This means you can visit the site anonymously using the Onion browser, especially if you live under an oppressive regime. Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see. Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions. The majority of the Deep Web is similar to the Surface Web, just less public.
Table Of Contents
The Deep Web houses web pages that are designed for restricted use and are protected by registration portals, paywalls, etc. These Deep Web sites are not indexed by search engines, making them impossible to find via traditional search engines like Google, Bing, etc. The Deep Web, which includes sites accessible via normal browsers but not visible to search engines, makes up a much larger portion of the Internet.
What Are EWallets And How Safe Are They?
There’s a significant risk to dark web users of being exposed to malware (malicious software) infections. There are several programs that hackers frequently use on the dark web. In darknet mode, you can select friends on the network and only connect and share dark web content with them. This enables individuals to form groups and only share content in a highly anonymous network of darknet users who they know. The advantages of I2P are based on a much faster and more reliable network.
With all the discussions related to hacking and exploit trading on the dark web, it is a great place to see where yet-unknown vulnerabilities are being discussed. By monitoring the dark web, users might gain the advantage of knowing where exploits are before they become widespread threats. Another problem with this system is that there’s increasing evidence that law enforcement agencies — such as the FBI — run and operate large number of exit nodes. This means that if you do anything illegal on the dark web and are unlucky enough to be routed through one of these nodes, the authorities will be well aware of what you’re doing. The dark web refers to the subsection of the deep web that provides illegal services. This runs the gamut from illegal substances to personal information, credit card details, child sexual abuse material and, allegedly, assassination contracts.
Passwords, physical addresses, bank account numbers, and social security numbers circulate in the dark web all the time. You may already be aware that malicious actors can use these to harm your credit, engage in financial theft, and breach of your other online accounts. Leaks of personal data can also lead to damage to your reputation via social fraud. All commonly public-facing websites accessed via traditional browsers like Google Chrome, Internet Explorer, and Firefox are contained here. Websites are usually labeled with registry operators like “.com” and “.org” and can be easily located with popular search engines. Privacy, which is usually provided by encryption, is another benefit of the deep web.
Certain details of your traffic can be intercepted at the entry and exit points of the node, by the people running those nodes, if they know what they’re doing and what they’re looking for. You’re also open to threats like end-to-end correlation attacks, so while Tor is a lot more secure and private, it’s by no means completely safe. As cyber threats evolve, having visibility into hidden layers of the internet is no longer optional—it is strategic. By combining security best practices with tools like search Deep Web engines, organizations can transform the Deep Web from a blind spot into a source of intelligence. The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web. In case of an attack, you can be sure that any of the data or information stored on your main computer will be safe.
In addition, there is always a malware risk in that uncharted territory. Consequently, using Tor (to visit the dark web) is something an average internet user does not do. And if you’re on that path, you better have reasonable explanations if it comes to that rare encounter with law enforcement. It’s mostly illegal, and some governments have their officials watching the dark web very closely for obvious reasons. In addition, just surfing the dark web can unleash malware on your computer. Besides, governments might actively monitor such activity, and anyone showing a keen interest in the dark web can become a law enforcement target.



