Even if someone intercepts the data, they’ll only see an encrypted stream between nodes – not your real IP. Unlike VPNs, Tor node operators don’t keep logs – this has been proven in court, including a major U.S. case against a hosting provider in 2022. Cybersecurity tools like CybelAngel’s external attack management (EASM) platform can help businesses monitor the dark web effectively. By providing real-time insights into threats, these tools enable companies to safeguard their brand and prevent data breaches before they occur. We may also see collaborations between state-sponsored gangs, pooling resources for more devastating attacks. However, rivalries over dark web marketplaces could also lead to turf wars, disrupting their operations and creating new risks for businesses.
Tor And The Onion Browser
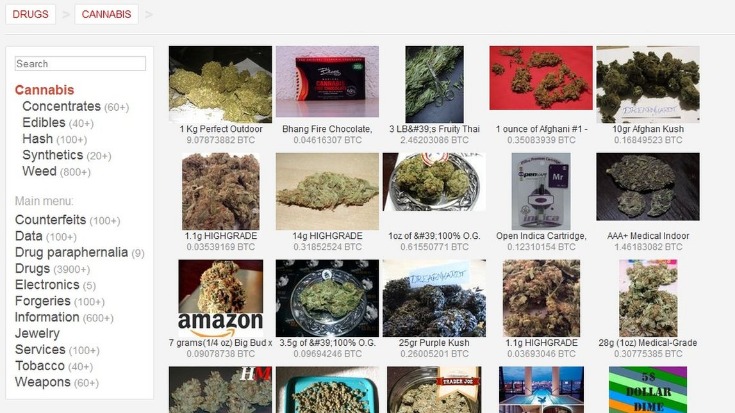
And cryptocurrencies add another layer of protection for those seeking to duck police suspicion. But like a never-ending game of whack-a-mole, law enforcement agencies around the world employ new tactics to stamp out anonymous markets, only to see new ones pop up. While you’re at it, now might be a good time to check whether any of your personal information has been leaked on the dark web.
In addition, its technology is open-source, and it doesn’t keep your data, which proves it is safe to use. This service lets you create your unique domain name with the letters or words you prefer. It has successfully become a replacement for AlphaBay Market, which was once leading the dark web transactions space. However, we do not recommend using this platform without taking proper precautions, such as anti-malware and a VPN. You can also use it on the surface web, but it is still unadvisable without proper safety measures.
In some countries, such as China and North Korea, the government uses heavy online censorship and blocks many dark web websites. This is where an Onion website, like the Tor browser, comes in handy. Hence, if you participate in them, whether knowingly or unknowingly, you can end up putting criminal charges on yourself, and in some extreme cases, even imprisonment. It will offer you an additional layer of encryption to access the deep parts of the internet.
Dangerous Software
Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though). The best thing is to actually understand how to find the fresh, new links. While this is not much compared to standard email services, it is enough for PGP-encrypted messages.
Fraud And Hacking Services
It operates in both French and English and has built a reputation for ease-of-use. Due to its extensive inventory and reputation for reliability, Brian’s Club has maintained a significant presence on the dark web. Quality and validity of the data it provides justify its higher cost over other marketplaces.
- Even one of the best search engines, called Grams, returns results that are repetitive and often irrelevant to the query.
- Besides, victims of crime may want to hide their identities from their perpetrators.
- These include weather forecasts, maps, calculations and Boolean operations as inclusion or alternatives among others.
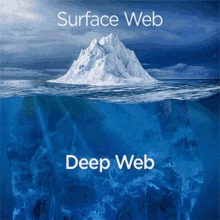
- These layers upon layers give this network its iconic “onion” name—as the onion itself has layers upon layers.
- Liam knows what he’s doing is dangerous, but he is addicted to drugs and hides his dependency from family and many of his friends.
Fraudulent Markets
These onion addresses will remain online even if the original page disappears. It also keeps the graphical copy and text of the page for better accuracy. You are not required to provide your personal information to create an account. The email service is available both on the surface and on the dark web. Check out these best onion sites to access the dark web securely and anonymously.
How To Stay Safe On The Dark Web
Other options include Ahmia and NotEvil, which focus on listing .onion links. Using the ProtonMail .onion site offers security and privacy advantages. Moreover, the company also uses HTTPS and SSL encryption on the Onion site for extra protection. This makes it even harder for third parties to see your email traffic.
What Are Hidden Services?
For example, there are separate categories for blogs, email services, file uploaders, forums, and more. I tested all the website links on The Hidden Wiki and almost all of them work (I was able to access sites like Deep Web Radio and ProPublica without any issues). The rise of cryptocurrencies like Monero and Zcash has further strengthened privacy, making transactions nearly untraceable. In addition to counterfeit merchandise, MGM Grand Market offers access to stolen credit card information, compromised bank accounts, and other financial fraud-related services. This marketplace specializes in a variety of illegal products, including drugs, counterfeit documents, and hacking tools. There are some darknet search engines mostly created by amateurs and they are very limited due to hidden services nature.
Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. However, there are some significant variances in the background despite the similarities. For example, Whonix’s virtual workstation machine connects to the internal virtual LAN. It can only interact with the gateway, the most effective method by which the browser protects user applications from learning a device’s IP address. While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings.

SecureDrop
- Wherever you are online, make sure you have trusted software protection to help keep you safer from the not-so-mythical cyber-monsters and online threats lurking there.
- One of the most straightforward ways to access to dark web safely is via Tor, so we’ve kept that in mind when compiling our list.
- Blockchain even has an HTTPS security certificate for even better protection.
- Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too.
- It publishes news in English and other major languages like Italian and Spanish.
A VPN encrypts the data traffic and keeps your activities private on the dark web. It also masks your IP address, making it difficult for government agencies to monitor or track your activities. We recommend using NordVPN as it offers top-notch security features, including dark web threat protection.

It is a Swiss-based company (privacy-friendly country), and all its tools are open-source, meaning anyone can test its vulnerabilities. When you access this site, do so with extra protection, even if you are technically anonymous when you use the Tor browser. We highly recommend using a strong VPN like NordVPN to stay safe and private. Later, the CIA released its onion website to provide worldwide access. Pitch is a dark web-based Twitter/X alternative, providing a secure platform for anonymous discussions and information sharing.