Your online activity and communications remain private and secret on the dark web. Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons. Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages. Some users also share links on encrypted apps like Telegram or Keybase that you can check.
Tips For Safe Access To The Dark Web
One of the key tools used on the Dark Web today was first released in 2002 – Tor, The Onion Router. Users gain greater anonymity online when using Tor because it encrypts Internet traffic and passes through several nodes. Government developed Tor so their operatives could remain untraceable. The Gray Web, Deep Web, and Dark Web are all valuable sources of threat intelligence, but many organizations limit their information-gathering efforts to the Surface Web.
Should I Only Use A VPN To Access The Dark Web?

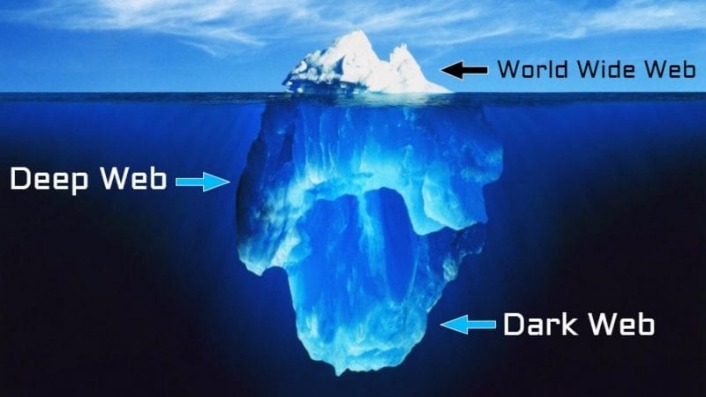
The darknet is a network, and the deep web constitutes the chunk of the World Wide Web that is beyond the reach of the search engines. So, we can decipher the dark web as the World Wide Web of the darknets like Tor, Freenet, etc. That is, the services and websites running on the darknet is the dark web. Although the Dark Web is often used for illegal activities, it’s not illegal to access it in many countries. Some people use the Dark Web for legitimate reasons, but prefer to remain anonymous.
These websites provide a platform for people to share information with the press without fear of repercussions. Although the dark web has a terrible reputation, there are plenty of legitimate reasons for accessing it. News providers like the British Broadcasting Company (BBC) host a mirror of their news site on the dark web so citizens in restricted countries can access unbiased news. This hidden copy of BBC News helps people in countries like China, Russia, Zimbabwe, and Vietnam access information privately. Company data that businesses store internally to manage operations and consumer data from inputted forms belong to the deep web. This data may include passwords, billing information, or purchase history—accessible to the user upon logging in but hidden from everyone else.
#2 Extra Protection
- For instance, your Gmail inbox and your Google Drive are part of the deep web because they don’t exist as publicly accessible domains.
- Law enforcement officials can exploit that weakness using “Tor-exit-node” monitoring techniques to expose users’ IP addresses and potentially trace activity back to the original users.
- The dark web isn’t just one sketchy marketplace hiding in a corner of the internet; it’s more like a messy, unregulated community with everything from freedom fighters to full-blown cybercriminals.
- The concept known today as the Dark Web set its foundation in the early 2000s.
- The Onion Router (Tor) also made the technology available in 2002.
The Tor Browser is the most popular browser for the dark web, but other popular options exist, like Brave, Comodo Dragon, Epic and SRWare Iron. If your incoming traffic passes through a node run by cybercriminals, they could inject malware into the response code. If your device is unprotected, you could be a victim of malware or a hacking attack. Though most volunteers mean well, others are malicious actors and surveillance agencies.
Hacking Groups And Services
Keep reading to discover the differences between the deep web and dark web and what they mean for your online safety. Funnily enough, they still own those traditional big channels of communication and there are still plenty of people following the same orientation as them. They just don’t like the fact that other opinions can also be heard nowadays.
The Dark Web Provides More Layers Of Encryption
While they’re related, knowing the difference can keep you safe from dangerous places on the internet and make you a hit at parties.
People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. The anonymity provided by onion routing comes at the cost of slowing your internet considerably. As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls. The biggest and most frustrating part about dark websites is that they live for a short span of time.
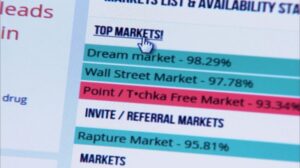
Dark Web Tools And Services
In fact, you probably already do it whenever you log in to a secured website. The dark web, on the other hand, makes up a tiny fraction of the internet as a whole. To access it at all, you need to use an anonymizing web browser such as “The Onion Router” (Tor) and a virtual private network (VPN). Later, we’ll delve deeper into how to access the dark web, but for now, you should just be aware that if you find yourself on a webpage and have no idea how you got there, it isn’t part of the dark web. For comprehensive protection against scammers, viruses, and ransomware across every layer of the internet, get Norton 360 Deluxe. For example, in 2016, investigative news outlet ProPublica launched a hidden version of its website on the dark web to provide a secure and anonymous way for readers to access its content.
Many web pages are dynamically generated or do not have links from other sites. Without links from previously indexed sites, the search engines cannot find them. That is why getting links from other pages is a basic principle of search engine optimization (SEO).

Are The Dark Web And The Deep Web Illegal?
If you engage in illegal activities or access illegal content that could implicate you in a criminal offense, you may face serious legal consequences, including fines and imprisonment. The dark web, a subset of the deep web, cannot be accessed with a regular browser. It hosts encrypted websites, often used for privacy, anonymity, or illicit activities. On the software end, the use of Tor and other anonymized browsers is not strictly illegal. In fact, these supposed “dark web” browsers are not tethered exclusively to this portion of the internet.
Challenges To Finding Dark Web Sites
Merely exploring the dark web out of curiosity or for research purposes is typically not a problem. Similarly, researchers and cybersecurity professionals often use the dark web to monitor emerging threats, leaked credentials, or underground discussions that could signal potential cyberattacks. However, these risks are similar to those on the surface web and the solution are the normal cybersecurity practices (secure connections, Multi-Factor Authentication, password managers, etc.). Phishing sites or malware can be used to gain access to your login credentials potentially leading to data theft or account takeover. However, there are several “.onion” search engines like “onion.city”, “onion.to”, and “notevil” that you can use to find suitable marketplaces. NordVPN offers a 30-day, no-risk trial subscription when you sign up on this page.