Gray markets buyers include clients from the private sector, governments and brokers who resell vulnerabilities. We need people who understand this even at a basic level so they can make good decisions for our future. For the last few decades, countries around the world have been watching the US to see how they should act when conducting digital espionage. When you have the US doing things like developing exploits and sabotaging nuclear enrichment facilities only to deny that they had any involvement with it, that’s what other countries will see and follow and do, too. Nations around the world now are acting like there’s no consequence for hacking into foreign nations or companies or people.
How Do I Verify Onion Links Safely?

These sites often look basic or outdated, and their URLs are lengthy strings of random letters and numbers. Keep in mind that visiting the dark web isn’t illegal, but engaging in criminal activity there is. That all is for general internet activities, you can guess how crucial having a VPN is when you hop onto something like the dark web. This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk.
Why You Need Automated Dark Web Monitoring
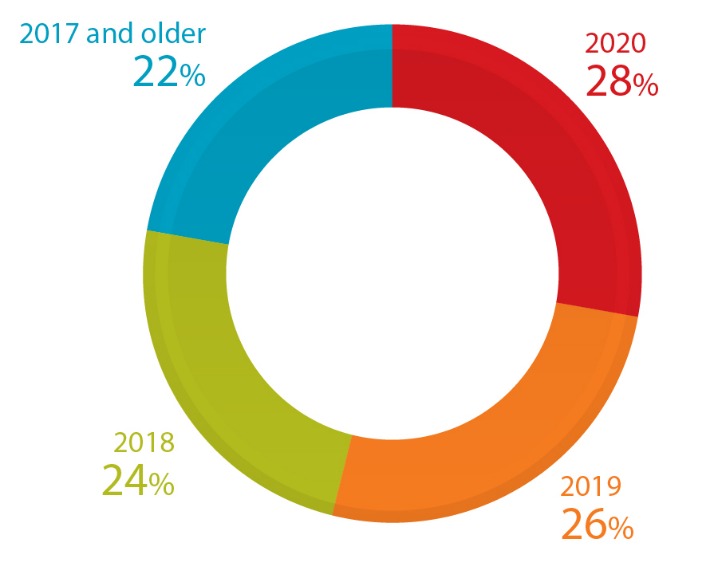
2024 was a significant year in the global high-profile fight against cybercrime. We at Kaspersky also actively contributed to law enforcement efforts to combat cybercrime. We also assisted the joint INTERPOL and AFRIPOL operation combating cybercrime across Africa. These and many other cases highlighted the coordination and collaboration between law enforcement and cybersecurity organizations. A series of law enforcement takedowns in the last few years have shaped the 2024 drug and fraud ecosystems. While 2024 was likely a record year for crypto crime revenue overall, darknet market (DNM) and fraud shop inflows fell, with DNMs receiving just over $2 billion in BTC on-chain, and fraud shops $225 million.
To counter law enforcement efforts at deanonymization, criminals frequently adopt tactics such as frequent username changes, disposable email accounts, and strict operational security (OPSEC) protocols. In many cases, they refrain from reusing wallet addresses for cryptocurrency transactions, as this can reveal patterns over time. By compartmentalizing their online activities and avoiding direct ties to personal identities, they reduce the risk of detection and arrest. This marketplace specializes in a variety of illegal products, including drugs, counterfeit documents, and hacking tools. These features help establish trust between buyers and sellers, providing users with a sense of security that many other markets lack.

Tor2(Run Out The Back)Door: Exit Scam Or Seizure?
As a user or cybersecurity professional, approaching these marketplaces demands utmost caution, thorough knowledge of operational security, and constant awareness of legal boundaries. Understanding both the benefits and dangers ensures safer interaction and more informed decision-making in an ever-changing digital environment. Transactions within these marketplaces typically leverage cryptocurrencies—most commonly Monero, Bitcoin, and privacy-centric digital currencies developed specifically to enhance transaction anonymity. Monero, in particular, has become the preferred cryptocurrency on the dark web in 2025 due to its advanced privacy mechanisms, which obscure transaction histories and wallet balances from public view. It comprises several forums, web platforms, and marketplaces usually hosted on encrypted networks and often run by independent groups or individuals. Dark web monitoring is done with the aim of high ethics as well as intelligence gathering.
Anonymity And Privacy
All data sourced from platform analytics, user reports, and darknet forums. Use hardware wallets like Ledger or Trezor for BTC/XMR—software wallets were hacked in 10% of 2024 cases. Generate fresh addresses per trade, encrypt backups with PGP, and avoid online storage, ensuring funds are safe on markets like ASAP.
RDP Global Admin Access

As more marketplaces emerge and established platforms seek new ways to conceal their operations, several trends are likely to shape the future of this clandestine economy. Dark web users rely on a combination of tools and networks to maintain their anonymity. Tor (The Onion Router) remains the most popular, routing data through multiple encrypted layers to hide users’ real IP addresses. Some individuals and groups also leverage I2P, a peer-to-peer network designed for continuous routing within a decentralized environment. Beyond these specialized networks, users often connect through VPN services and proxy chains to further mask their physical locations. The Darknet is in constant flux, shaped by technological innovations, shifting user behaviors, and law enforcement crackdowns.
- These markets sell a range of illegal goods and services, including drugs, weapons, stolen data, and counterfeit items, and they typically require special software like Tor for access.
- Reputable actors active on this forum are often very sophisticated, acquiring a portfolio of positive reviews over the years.
- The below screenshot is one of the above products and advertises as, “Pre-Shredded Cash 25,000 USD Cash” and is for sale for $999.00, which was discounted from an original price of $2,100.00 USD.
- Dark-web marketplaces attract sophisticated cybercriminals adept at launching phishing scams, malware attacks, or ransomware threats.
- Regular training can ensure your team is aware of the latest phishing techniques and other threats.
- Their design mirrors legitimate e-commerce platforms, but their operations revolve around illegal products and services.
Common Categories Of Illicit Content
- The forum has additional sections and threads that are hidden and can only be accessed through paid membership for a premium account.
- Many breaches are the result of successful phishing attacks, making human error a significant vulnerability.
- Transactions are conducted through Bitcoin and Monero which provides anonymity for both buyers and sellers.
- Like a lot of other forums in a similar domain, Pitch is significantly focused on corporate access, hacking, and data leaks, making it a communication hub where hackers and cybercriminals gather.
- Experience Flare for yourself and see why Flare is used by organization’s including federal law enforcement, Fortune 50, financial institutions, and software startups.
Multi-layered DDoS protection countered 2024 attacks, maintaining 97% uptime—the highest in our rankings. Its 99% escrow success rate resolves disputes in 24 hours for 95% of cases, securing its 20% market share. Archetyp uses AES-256 encryption with PGP, mandatory since a 2022 phishing scare, securing its 12,000+ users.
Many darknet marketplaces employ the use of specific cryptocurrencies (such as XMR) that use technologies such as stealth addressing and ring signatures to evade traceability. However, these currencies, due to their decentralised and counter-economic nature, are often restricted by centralised platforms from purchase and practical use. The results of that investigation were published in a report called Technical analysis of the Genesis Market.
The forum has specialized in connecting the initial access brokers to the buyers who want to buy that access. Also, it offers discussions about software vulnerabilities, malware, and leaked databases. Its popularity can be as a result to the ease of use on it, as the forum features a clean and accessible design with enhanced moderation and a wider scope of the leak topics and sources.
The Increasing Risk Of Data Breaches
Tor offers secure and encrypted access to the dark web forums, ensuring that the user’s IP address is hidden and difficult to trace. Therefore, cybercriminals use these forums because they offer assured anonymity and security. Perhaps one of the major attraction factors of these forums is undoubtedly anonymity. Cybercriminals want to carry out their illegal activities without detection by law enforcement agencies and other authorities.
CryptBB focuses on the exchange of advanced hacking tools, stolen identity logs, and various exploitation techniques. The forum doesn’t have a mass recruitment structure or flashy marketing, but it’s still a prominent player that needs to be monitored for general users’ safety online. DarkForums rose to power almost immediately after the original version of Pompompurin was shut down after the FBI arrested the infamous hack forum’s administrator. The forum offers leaked databases, malware, auto-checkers, lists of stolen credentials, account hacking tools, and several other threats.
Products And Services
While it might be tempting, remember that downloading such content has serious legal and cybersecurity risks. Some sellers offer cracked versions of expensive software that you’d typically pay hundreds of dollars for. Others sell pirated eBooks, academic materials, and entire premium courses ripped straight from paid platforms. Unfortunately, the dark web hosts not only explicit but also deeply illegal and disturbing content. The markets often share materials related to child exploitation, pornography, and non-consensual recordings, all of which are serious crimes that inflict lasting harm on real-life victims.