A top-of-the-line VPN network that ensures maximum security while accessing dark sites online. NordVPN is one of the best VPNs to combine with the Tor browser whenever you want to surf dark sites. It offers top-of-the-line security and fast speeds for a smooth browsing experience on the dark web. Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web. As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing. All in all, it is not illegal to access the dark web, but it can create issues for you.

Install AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web. Download AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web. Your IP is still being revealed to one of the nodes in the onion, meaning your activity and identity can be unmasked. Archive.today collects snapshots of websites and archives them for later viewing. If this sounds similar to The Wayback Machine, the concept is indeed the same. However, The Wayback Machine allows website owners to block their sites from being archived, while archive.today does not.
Keep Tor Browser Updated
Kilos allows you to search across six major dark web marketplaces, offering a broader scope than its predecessor, Grams. Unlike some dark web search engines, Candle does not overwhelm you with advanced settings or filters. Instead, it provides a streamlined experience that prioritizes usability. This makes it a great choice for beginners exploring the invisible web for the first time. The search engine delivers unbiased search results by avoiding personalized algorithms. This ensures that you receive the most relevant information without being influenced by your browsing history.
If you pair the regular DuckDuckGo engine with the Onion version, you can perform an entire web search. Unlike Google, Pipl can interact with searchable databases, member directories, court records, and other deep internet search content to offer you a detailed snapshot of a person. The deep web is made up of content that typically requires some form of accreditation to access. Examples include library databases, email inboxes, personal records (financial, academic, health, and legal), cloud storage drives, and company intranets.
Use A VPN
- This runs the gamut from illegal substances to personal information, credit card details, child sexual abuse material and, allegedly, assassination contracts.
- The search engines listed above are the best deep web search engines for exploring the invisible web.
- Make Tech Easier provides tech tutorials, reviews, tips and tricks to help you navigate the complicated world of technology.
- Accessing the Invisible Web generally involves using specialized search engines or browsers such as Tor.
- On The Internet Archive, you are going to have access to things such as movies, music, etc. that I mentioned earlier, but you can also enjoy printed materials.
- It works by sending internet traffic through volunteer-operated nodes all over the world.
Sci-Hub gives access to millions of scientific papers, mostly ones from behind paywalls. However, due to copyright infringement, Sci-Hub is considered illegal and banned in many countries. Impreza Hosting is a service that helps you host a site on the Tor network. It provides an .onion URL and an interface for you to manage your Tor site easily. It also boasts that no personal information is required to use the service, and payment can be made with cryptocurrency. One of the most popular ways to get around the dark web is not to use a search engine at all.

H4: Personal Data Gathering
Apart from Tails OS, Qubes allows the highest secure connectivity for virtual machine systems. It’s a lesser-known but highly effective unrestricted search engine ideal for in-depth exploration. Since activists, journalists, and advocates need the dark web to communicate securely, find evidence, and bypass censorship, it remains a tool for privacy and free expression.
Quick Comparison Table: The Dark Web Search Engine Features
Many social media platforms keep their presence on the dark web, and it is no surprise that Facebook has a .onion portal. Facebook’s dark web version allows users to access the site where it is banned or restricted. Although the social application is known for collecting data on its platform, it does not like sharing the information with others. It is the dark web’s version of Wikipedia with a massive links directory.
How To Access The Dark Web Safely
- You can enjoy things such as almanacs, encyclopedias, an atlas, and biographies.
- This engine uses information from publicly sourced sites (such as Wikipedia) with the aim of increasing traditional results and improving relevance.
- Phobos is a very minimalistic and simple search engine for Tor .onion hidden websites.
- Use categorized directories or reputable search engines to reduce the chance of clicking on spam or malicious links.
- It means they search for .onion websites through automated means but also allow users to suggest new sites, most often anonymously.
- Torch stands out for its commitment to user privacy, as it doesn’t store search history or collect any user data, ensuring higher anonymity.
After all, ProPublica isn’t afraid to take on controversial topics like child labor and political corruption. Haystack has a BSD license, supports Solr, Elasticsearch, Whoosh, and Xapian, and works well with third-party programs without requiring source modification. You may create your search code once and then choose whatever search engine you want it to run on with Haystack.
Ensure Compatibility With Privacy Tools
However, while browsing the dark web itself is lawful, taking part in illegal activities — like buying or selling illegal goods or engaging in criminal behavior — is not. To stay on the right side of the law, be cautious about what you access and ensure you follow the rules in your region. Deep Search is an open-source dark web search engine designed to index and explore onion space, the hidden services within the Tor network.
According to its functionality and quality, it is highly competitive with its competitors. The options for topics to search for are endless, and you can even customize it to enhance your experience. The Wayback Machine is a front end to the Internet Archive’s gathering of open Web pages in the Deep Web Search Engine family. It incorporates more than 100 terabytes of data—a colossal gathering with immense stockpiling prerequisites. A search for alxxxol returns results of alcoholics, and anonymous groups, rather than say, a Wikipedia page on what alcohol is for example.
The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential. It is a good way to prevent third parties from tracking online activities. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web.
To explore it, you need special tools like the Tor browser (short for The Onion Router) and search engines designed specifically for the dark web. While some .onion sites provide essential services like secure communication and censorship-free journalism, others spread malware or run scams. With this in mind, finding verified links is crucial for avoiding threats on the dark web.
What Is Kubernetes And Containers? Why Is So Popular?
“Using Forest VPN with Tor has been a game-changer for accessing the dark web safely. The peace of mind that comes from knowing my data isn’t being tracked is invaluable. Plus, the energy-efficient design means I can browse longer without worrying about battery life.” – Alex, a privacy advocate. More importantly, you should now know how to access these hidden sectors of the internet at your leisure. Websites that exist purely on the deep web have different access, so there’s a level of privacy for the website hosts that isn’t possible on the regular internet. If your website is only accessible through the deep net, tracking down the physical location of your servers is much harder than it would be for a regular website.
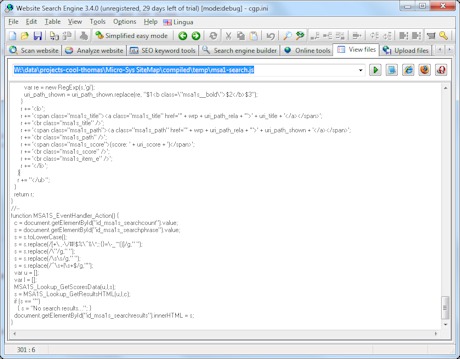
Part of what makes the dark web the dark web is that you can’t access it through your normal web browser, nor can you look something up on it via a Google search. If your team can find stolen credentials as soon as they appear on the dark web, you can be proactive about preventing an attack with specialized dark web search engines. Security teams can leverage automated Threat Exposure Management solutions to monitor sources across the dark web, including forums and marketplaces, as well as other sources like Telegram. These website name.regular search engines do not use index onion domains, so you can only access Dark Web with special TOR software.



